Sites claiming President-Elect Barack Obama will refuse to take the oath of office Tuesday are serving up attack code believed …


Sites claiming President-Elect Barack Obama will refuse to take the oath of office Tuesday are serving up attack code believed …

Computer systems at three London hospitals remained down on Wednesday morning after PCs were apparently infected with malware. No patient …

Computer systems at three London hospitals remained down on Wednesday morning after PCs were apparently infected with malware. No patient …

The company showcases its unified cyber security platform to reshape the digital future of the UAE.

Coveware by Veeam will bring industry-leading cyber-extortion incident response services and proactive enterprise preparedness to Veeam’s existing ransomware protection and recovery capabilities. Coveware will offer forensics and remediation capabilities through the Veeam Data Platform, as well as proactive services to Veeam Cyber Secure customers.

The SANS CISO Network will also take place during GISEC, with an opening keynote from H.E Dr. Mohamed Al Kuwaiti, Head of Cybersecurity for the UAE Government and Cyber Security Council.

Visit ESET at GISEC 2024 at B79 in Hall 6 to discover the future of cybersecurity and embark on a journey towards enhanced cyber resilience and peace of mind.

Positive Technologies detects a series of cyberattacks against government organisations in Russia and the CIS.

OPSWAT Deep Content Disarm and Reconstruction (Deep CDR) scores 100% Protection and Accuracy Score, validating its effectiveness in protecting against file-based threats.

Terry Young, Director of Service Provider Product Marketing, A10 Networks explores the most pressing attack vector for organisations to be aware of in the coming months.

Kaspersky has exposed a new phishing campaign targeting small and medium-sized businesses. The attack leverages the email service provider SendGrid …

Edwin Weijdema, Field CTO & Lead Cybersecurity Technologist at Veeam Software, discusses how cyber insurance has become an increasingly popular …

Human-centric threats continue to impact organisations in the UAE, with reports of direct financial penalties due to phishing up 44% and reports of reputational damage up 300%.
Presented by Sertan Selcuk, from OPSWAT, the discussion titled Zero-Trust Approach to Protecting Critical Environments delved deeply in an analysis of decades of company data and insights.

AI-driven SOC Insights analyzes vast amounts of threat and network data to identify what matters most, provides actionable insights, and drives automation with the broader security ecosystem for rapid remediation and containment.

Emad Fahmy is currently the Systems Engineering Manager at NETSCOUT. In this op-ed he discusses how packet data can support the crucial task of protecting digital landscapes from cybersecurity threats.

Ongoing Malicious Campaign Impacting Azure Cloud Environments, Proofpoint Reveals.

After an encouraging decline in 2022, the ransomware landscape saw a major escalation in the frequency, scope, and volume of …

Dave Russell, Vice President, Enterprise Strategy at Veeam explores how zero trust security processes have evolved in recent years and how in a landscape where the benchmark for security is constantly shifting, zero trust must continue to adapt in order to survive.
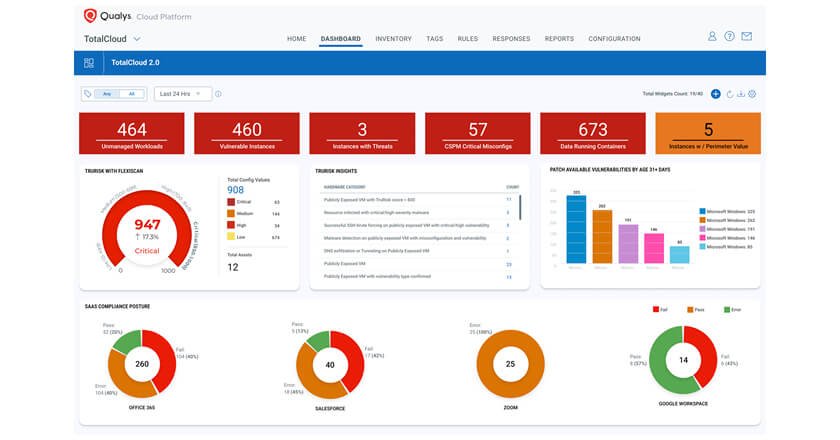
Expanded solution brings cloud infrastructure, SaaS apps and externally exposed assets together for a unified view of risk across multi-cloud environments.