According to AccessData Group, the Middle East is fast becoming a prime target for cyber criminals, mostly because so many …


According to AccessData Group, the Middle East is fast becoming a prime target for cyber criminals, mostly because so many …

Pirated software is costing industry in excess of $114 billion, according to a new IDC survey commissioned by Microsoft. Though …

Experts recently pointed towards security as the main obstacle for adoption of all cloud types and claimed that cloud security …

Oracle released emergency patches for Java on Monday to address two critical vulnerabilities, one of which is actively being exploited …

Dell on Monday unveiled its SonicWALL SuperMassive 9000 Series next-generation firewall. The solution provides advanced threat protection at multi-gigabit speeds …

Companies with IT security strategies that focus mostly on complying with key standards are dangerously unprepared for emerging cyber threats, …
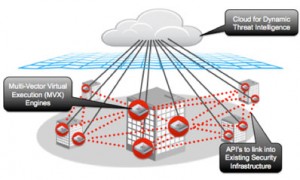
Security company, FireEye, has announced a new threat protection platform designed to help enterprises deploy new security models to counter …

Dell SonicWALL’s Head of Product Marketing, Florian Malecki, talks devices, data, and security. We love our devices. IDC is predicting …

McAfee on Monday announced that it has acquired the ValidEdge anti-malware sandboxing technology from LynuxWorks in order to add a …

Researchers from Symantec have found and analysed a version of the Stuxnet cyber sabotage malware that predates previously discovered versions …

HP on Monday unveiled its Big Data Security strategy, describing how combining the enterprise search and knowledge management resources from its Autonomy subsidiary …
Times have never been better for security-focused channel partners. The fast changing threat landscape and the emergence of advanced threats …

With the news that some Apple, Facebook, and Twitter employees’ Macs were hacked, as well as Apple and Oracle’s subsequent software …

Google on Thursday unveiled the $1,299 touchscreen Chromebook Pixel, a pricey slab of hardware that runs Google’s Web-centric Chrome OS, but defies …
Another day, another critical security exploit discovered for Adobe Reader. The PDF software’s near-ubiquitous presence has made it a big, fat, …
The head of the malware analysis team at antivirus vendor Kaspersky said last week that a recently found exploit that …
The security issues affecting businesses are similar around the world, writes Florian Malecki, Head of Product Marketing Manager –EMEA, Dell …
Karl Driesen, VP EMEA, Palo Alto Networks
Today’s mobile spam and phishing attacks will increasingly delivered by mobile malware networks, despite mobile device operating systems being more …

So far, the evidence suggests Windows 8 has hardly been the gleaming success that Microsoft no doubt hoped it would …