The advent of mobility and its infiltration on enterprise has birthed a whole new type of security risk, and as …


The advent of mobility and its infiltration on enterprise has birthed a whole new type of security risk, and as …

Cyber criminals are increasingly using .eu domain names in their attack campaigns, according to data from multiple security companies. “Numerous …

In its November 2012 Blue Coat Mobility Study, the company surveyed 350 respondents and found that most organisations allow employees …

Xerox and McAfee revealed new protection against malware and viruses with the first networked multifunction printer to use McAfee Embedded …
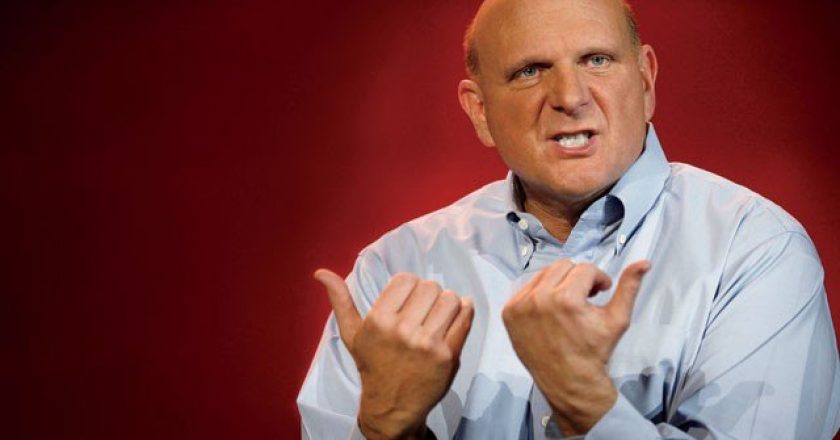
Microsoft CEO Steve Ballmer has branded Android ‘wild’ and Apple too ‘controlled’. During a recent conversation with LinkedIn Co-Founder Reid …

With the advent of mobility and the influx of BYOD in enterprise, employers are struggling to keep control of their …

Google’s new app scanner in Android 4.2 Jelly Bean moves the platform closer to Apple’s model of vetting software before …
EMC has today announced it has signed a definitive agreement to acquire privately-held Silver Tail Systems, which provides real-time web session intelligence …

With the problem of hacking and its consequences on enterprise only exacerbating, CNME rounds up the views and tips from …

Research and advisory firm, Gartner, has released its list of technology predictions and trends for the years 2013 and beyond. …

A researcher at North Carolina State University has uncovered a vulnerability that could be exploited to send deceptive text messages …

Some cloud providers fail to detect and block malicious traffic originating from their networks, which provides cyber criminals with an …
Security vendor AccessData has launched version 2 of its CIRT (Cyber Intelligence and Response Technology) product, which is the only …

CoDeSys, a piece of software running on industrial control systems (ICS) from over 200 vendors contains a vulnerability that allows …

Several high-profile security breaches around the world grabbed the attention of the Middle East IT industry, but it has taken …

A team of researchers from two German universities has released a study asserting that many of the most popular free …

Cyber criminals are using computers infected with a particular piece of malware to power a commercial proxy service that funnels …

Mobility has changed the whole landscape of the enterprise. People now want to be able to work from anywhere, at …

Iran’s claim that its domestic Internet system suffered a slowdown from a heavy cyber attack is possible, but knowing for …

A cyber gang thought to be based in Eastern Europe and the former Soviet Union is recruiting dozens of people to participate …