A security firm has revealed it has managed to decrypt files damaged by the recent Petya ransomware attack, on one infected computer.
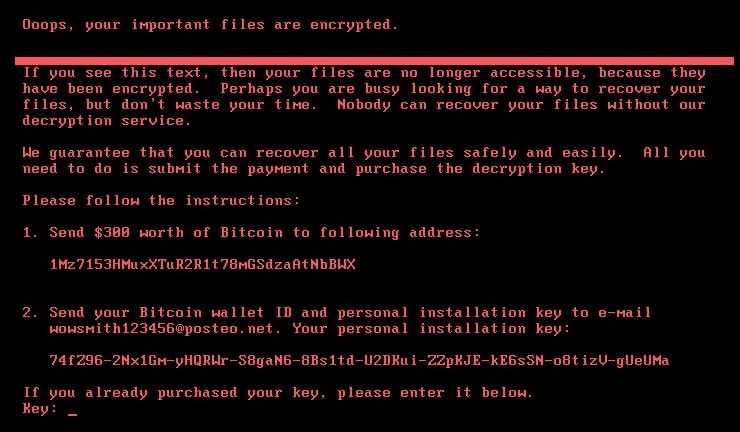
The malware has been linked with a large number of infections that hit businesses around the globe – a significant proportion of which (around 60 percent according to statistics published by Kaspersky) affected machines in Ukraine.
The potential solution, created by Positive Technologies, is said to only work if the ransomware secured administration privileges to the machine.
However, the company has also said the concept is currently too technical for most average computer users to run.
Dan Tara, the firm’s executive vice president, told the BBC, “Once you have a proof of concept of how data can be decrypted, the information security community can take this knowledge and develop automatic tools, or simplify the methodology of getting the encryption reversed.”
The company says in a blog that the creators of the ransomware made mistakes in programming the encryption algorithm Salsa 20 that was used with administration rights.
Salsa20, which activates when the ransomware has admin privileges, corrupts a device’s Master File Table (MFT), meaning that files are lost forever.
Tara said his team had not expected to get this result when it started investigating the outbreak.
Head of Reverse Engineering Dmitry Sklyarov, said, “Recovering data from a hard drive with this method requires applying heuristics, and may take several hours.”
He added, “The completeness of data recovery depends on many factors (disk size, free space, and fragmentation) and may be able to reach 100% for large disks that contain many standard files, such as operating systems and application components that are identical on many machines and have known values.”
The research team’s finding only works on the recent Petya ransomware and its variants.





