The cloud is everywhere today. However, many organisations as well as individuals still don’t fully trust the nature of the cloud. Security correspondent Daniel Bardsley speaks to experts about the risk perception and privacy challenges of the cloud.
No brand is more iconic than Coca-Cola, a beverage powerhouse with a global reach that, despite growing health concerns over sugar-rich fizzy drinks, helped its parent firm to make profits of more than $1 billion last year.
Coca-Cola may trace its history back to the 19th century, but The Coca-Cola Company is not stuck in the past: in today’s digitised world, cloud computing is playing a central role in streamlining the production and distribution of the household-name drink.
“We wanted to use the cloud because we wanted to automate everything – from the moment we make the bottle to reaching the customer,” says Luciano Ludwig, a system solution architect for The Coca-Cola Company.
Headquartered in Atlanta, Georgia, The Coca-Cola Company has developed a cloud-based system involving NetApp HCI, a hyper-converged infrastructure produced by NetApp, the Californian-based cloud data services company.
Ludwig, speaking to Security Advisor Middle East at the recent NetApp Insight 2018 event in Barcelona, the cloud data services company’s annual gathering for EMEA, says the automation extends even to ensuring that delivery trucks have fuel to reach businesses that require the drinks.
The programme that Ludwig has been involved with “didn’t find any security problems” linked specifically to the use of the cloud.
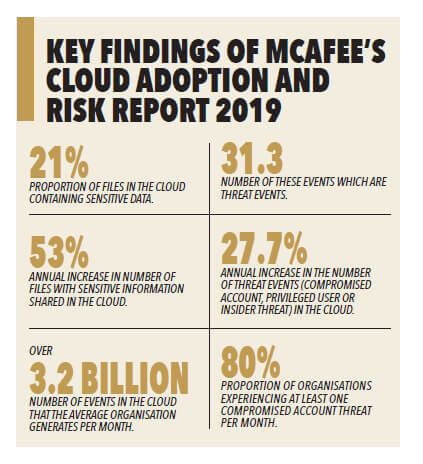
However, the recently released “Cloud Adoption and Risk Report 2019” from the cybersecurity provider McAfee highlights a range of cloud-related potential security issues.
A key finding of the report is how many files with sensitive data are now being shared in the cloud, with the number having increased 53 percent year-on-year. What is behind this increase?
“There are now more cloud applications for businesses to store information in than before. There are many HR applications and healthcare applications that are cloud-based,” says Nigel Hawthorn, McAfee’s spokesperson for EMEA.
“But there’s a second, perhaps more hidden, reason: we as individuals are trusting the cloud more than before.
“As data increases generally because of the merging of personal and business life, our own information – financial information, health information, photocopies of passports – are also in the cloud because we recognise that’s where data is often stored.
“I, as an individual, have a lot more data in the cloud. That’s not necessarily a bad thing but it’s data that we wouldn’t worry about controlling before.”
Hawthorn says the problem is not the fact that the data is in the cloud, but that it may have been shared with someone with whom it should not have been shared.
It is easy to share files, but also easy to share a folder and, a few months later, to add more files to that folder, or to share a folder while forgetting that it contains another folder with sensitive information. In these ways information gets shared almost unintentionally.
“It’s not down to IT on their own. Employees have to take their responsibility, but they need to be trained to understand the issues,” says Hawthorn.
A dramatic finding of the report is the huge disparity between the number of cloud services that companies think they are using – the average is 31 – and the actual number, which is 1,935.
Hawthorn says people sometimes look at him in disbelief when they hear figures like these. But if services such as pdf converters and booking systems for hotels are taken into account, it becomes easier to understand why the numbers are so high.
“All of these are typically cloud services where somebody may well choose to upload information without thinking about the securing issues around that,” he says.
“The biggest question for every IT manager is, ‘What’s that gap? There’s over 1,000 services I didn’t know about. What are they? What are they being used for? Are they low or high risk? Are they OK for my users to use?’
“In the Middle East, where people typically think cloud is less used, when we’ve done tests we’ve also found at least 1,000 different services.”
As enterprises move to the cloud “very fast”, after what could have been decades of security measures for an on-premises network, Hawthorn says they must ask questions of themselves.
“Are you going to keep these same policies and processes when moving data to the cloud? It can be done, but you need to think that, in your rush to the cloud, you don’t forget to have these security measures installed,” he says.
A common concern over cloud services is that users rely too heavily on cloud providers to deal with security. Hawthorn reminds users that cloud service providers are responsible for the “low-level security”, which includes patching the operating system, connectivity and the servers.
“But don’t let that lead you into a false assumption that everything is the responsibility of the cloud service provider,” says Hawthorn.
“It’s always the company’s responsibility to decide which users can use it; it’s the company’s responsibility to have data loss prevention if they want to.”
 An increasingly popular technology for highlighting potential cybersecurity breaches is behaviour analytics, which uses artificial intelligence to analyse past activities. This, in turn, can identify unusual events that could indicate fraud.
An increasingly popular technology for highlighting potential cybersecurity breaches is behaviour analytics, which uses artificial intelligence to analyse past activities. This, in turn, can identify unusual events that could indicate fraud.
“The company has five years of data on me and the devices I use, the cloud services I use, the amounts of data I put there and use, the countries I visit,” says Hawthorn.
“In the last five years I’ve been to the USA and all around EMEA, but I haven’t been anywhere in Asia. If, all of a sudden, I try to log onto an Android device in China, two things pop up: I’m in a different country and I’m using a different application. It’s strange behaviour; let’s force them to re-authenticate.”
THE HYBRID CLOUD AND MULTI-CLOUD
At the recent NetApp Insight 2018 event in Barcelona, multi-cloud and hybrid cloud environments are at the centre of discussions.
Multicloud is a common arrangement involving the use of more than one public cloud provider. For example, the majority of Amazon Web Services (AWS) users also make use of Microsoft’s Azure technology. When third-party public clouds and on-premises private clouds are used together, the term hybrid cloud is used.
What cybersecurity vulnerabilities, if any, do these arrangements create?
Kirk Ryan, a lead cloud solutions architect at NetApp, does not think they present risks in themselves. However, as cloud environments become more complex, he does have concerns over the potential for a “skills gap” over how to deal with the myriad threats that exist. It can be difficult, according to Ryan, to learn the various security protocols of more complex set-ups.
“For example: does the team doing AWS as well as cloud on-prem know how to monitor that?” says Ryan.
Nigel Hawthorn of McAfee says that more complex arrangements such as hybrid clouds require organisations to look for potential problems in multiple places.
“You need to look at all your cloud environments, both private and public, to try to ensure that you’re putting in the security measures that you need,” he says. “I recommend having a system that provides a holistic view of cloud services, which makes securing such environments more effective and easier to manage.”





