CNME Editor Mark Forker managed to secure an exclusive interview with Charl van der Walt, Global Head of Security Research at Orange Cyberdefense, to find out more about the key trends and new threats that emerged from their comprehensive Security Navigator Report 2022 – and has called for the cybersecurity community to review and re-evaluate the way it thinks about the actual crime committed through cyber extortion, rather than just the technical aspects of the attack.
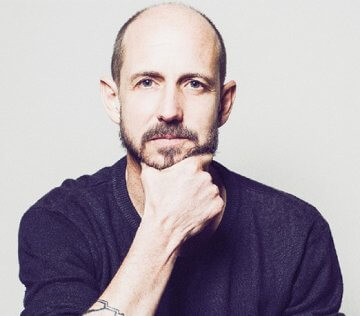
Charl van der Walt is undoubtedly one of the most revered and respected thought leaders in the global cybersecurity ecosystem, and in his position as Global Head of Security Research at Orange Cyberdefense, he has been able to leverage his knowledge and expertise to equip his customers with the ability to protect themselves amidst an increasingly unpredictable and constantly evolving threat landscape that we currently find ourselves immersed in.
In a candid and forthright interview with CNME Editor Mark Forker, he fleshed out some of the key insights from his perspective that emerged from their Security Navigator Report 2022. He described the sheer volume of attacks that are occurring every month as ‘extraordinary’.
“One of the first things we attempt to do with the report is normalise the volume of incidents across our customers to determine if they are increasing or decreasing. In the end, we concluded that they have increased by 13%, and that essentially means that on a normalised basis each of our customers deals with 42 confirmed incidents per month. This is the average and incidents tend to vary based on the scale of our deployment. Now that doesn’t mean the incidents are necessarily a compromise but it is a confirmed security failure. It really strikes me as an extraordinary amount of work to have to respond to 42 incidents every month,” said Van der Walt.
He explained how the relationship between Orange Cyberdefense and its customers works, and again expressed his dismay at some of the findings and figures that came to light during the report.
“We have a very specific perspective because we are a service provider. We have these detection systems that are spread out across our customers and then they trigger, and then we proceed to triage them. It’s our job to determine why did they trigger, was it a false positive, can we put it down to some benign thing – and only then when we are genuinely convinced that this is an indicator of an attack, or compromise, do we contact the customer. Those 42 incidents every month is only about 36% of the incidents that we deal with, so if the customer was doing it themselves then they would be dealing with three times that number, which also strikes me as extraordinary, and quite frankly I find it very disheartening,” said Van der Walt.
Interestingly, Van der Walt also highlighted that despite the many technological advancements that have been made in cybersecurity in terms of detection techniques and practices, it still is extremely difficult to determine what sort of attack is going on within your IT environment.
“It really is difficult to know what you are looking at when you get these alerts, because despite applications like MITRE ATT&CK and all the other progress that we have made in this space, it remains very difficult to know whether a given indicator really represents an ongoing attack, a real attack, or just something benign,” said Van der Walt.
He also criticised the industry’s overall approach to security, using the needle and the haystack analogy to describe an approach he deems largely ineffective and expensive.
“The sheer volume of energy that goes into trying to figure out was this supposed to happen or not is incredible, and part of that is due to the narrative that is being put forward by our industry, which is this view that we can’t really defend ourselves, so we need to be able to detect, therefore let’s put things down everywhere that tell us when something is going on. We spent a lot of time last year debating an observation on what we call the ‘false positive ratio’. We found that in our bigger clients the false positive ratio was much higher than our smaller clients, and my conclusion was that our bigger clients were putting more stuff related to detection in and, as you put more in, then your ROI starts to drop off. Essentially you are seeing more in total, so that’s a security win, but bad things and things that are actually benign are still very hard to tell apart,” said Van der Walt.
There were a range of interesting statistics to come from the Orange Cyberdefense Security Navigator Report 2022, but another that jumped off the page for Van der Walt was the fact that over half of those recorded security failures every month were not caused by those with malicious intent.
“One other thing that I found hugely interesting from the report was the ratio between incidents and accidents. We discovered that a lot of these incidents do not originate with someone outside the business with malicious intent, they originate from someone inside the organisation and that’s about a 50/50 split. What that means is basically half of those 42 incidents are not caused by something the attacker is doing, but instead your users making mistakes,” said Van der Walt.
Van der Walt then talked about the way in which the cyber community talk about cybersecurity attacks, and he pointed out that we largely ignore the element of criminality within them. He revealed that as a company they underwent an exercise of trying to apply existing theories of crime to cybercrime – and revealed that they have had a lot of success in examining the problem of cybersecurity through the lens of these much older disciplines that consider why crimes happen and how you can counter it.
“One of the things that emerged is what criminologists describe as victim suitability, which means how suitable is the victim to the offender and what factors come into play for an offender when they are considering who they are going to steal from. There is an acronym they use to summarise what makes a victim suitable and it is called VVIVA – Visibility, Vulnerability, Inertia, Value, and Access. Visibility is all about online presence and attack surface size, so effectively how many systems you are pushing online. Vulnerability speaks to cyber hygiene in terms of patching and passwords and Access basically means the ease and time allowed to an offender in cyberspace and how capable are we in reducing the attacker’s dwell time,” said Van der Walt.
According to Van der Walt, much of VVIVA is instinctive and relatively obvious but he found Inertia and Value and their connotations especially interesting.
“Inertia basically means that big things are harder to steal than smaller things – and if you relate that to cyberspace then that would equate to the ease at which the attacker can not only exfiltrate stolen data, but also (in the military sense of the word) exploit that stolen data. The big question is whether they can really access and interpret the value of something they have stolen,” said Van der Walt.
Looking at Value, Van der Walt linked this element to the ongoing ransomware crisis that is engulfing the cybersecurity ecosystem on a global scale.
“Given that the dominant form of cybercrime right now is extortion, which we have seen in the form of ransomware attacks, the value that we are looking at is not the value of the stolen assets to the attacker, but instead the value of the stolen assets to the victim. Anyone, no matter how small or unimportant, can be extorted if they have data or systems that are important to them,” said Van der Walt.
He outlined in more detail why it is valuable to view cyber extortion as a criminal act as opposed to a technical security failure of your IT system or environment.
“With cyber extortion one of the reasons it is very interesting and valuable to think about it as a crime, rather than a technical problem is that forces you to think about the entire journey of that crime. The crime typically starts with an initial access broker, who is hunting for vulnerable systems to compromise – then those compromised systems, or companies are traded with affiliates, who perform the lateral movement, encryption, and data exfiltration and then it passes to the so-called ransomware operator who does the extortion. The final crime is the extortion. It’s in the negotiation between the offender and the victim for something that the offender has stolen, and the victim needs. That’s the core and the essence of it, the essence of it is not in the deployment of malware to encrypt the data, it is all in the negotiation,” said Van der Walt.
“Fundamentally, cyber extortion is first a problem of crime and ultimately has to be addressed as a crime. This means that every business that has something of value to them is a potential target. The good news is that businesses can take positive steps to make themselves less attractive to offenders and the frontline of defence is addressing the VVIVA variables.”





