Inaugural global study finds 49% of UAE organisations are not fully confident their AI security controls would detect compromised AI …


Inaugural global study finds 49% of UAE organisations are not fully confident their AI security controls would detect compromised AI …

New Nuclei Suite delivers archiving, AI-driven communications intelligence and optional lexicon-free supervision in a single platform with cost-effective licensing.

Acquisition of AI security innovator positions Proofpoint as the first cybersecurity platform to comprehensively address agentic workspace protection at the intersections of humans, data, and AI.
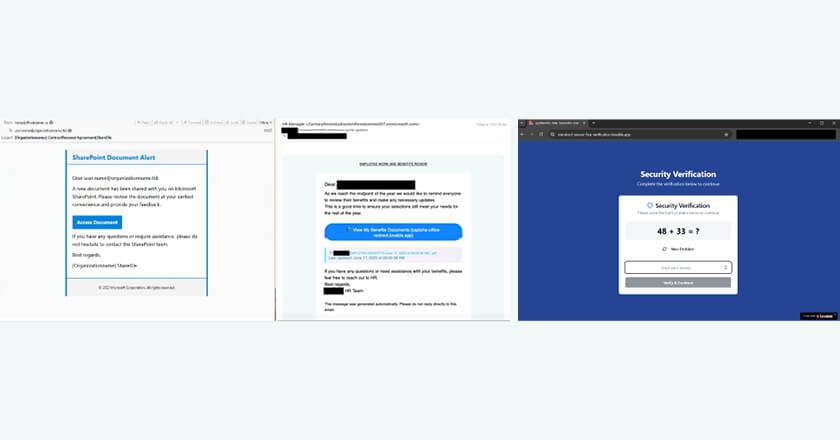
Threat actors are increasingly using an AI website generation platform to create fraudulent websites for credential phishing and malware delivery.

New Proofpoint Report Reveals Sharp Rise in URL-Based Threats, 400% Spike in ClickFix Malware Campaigns and 4.2M QR Code Attacks.

Strategic acquisition marks significant milestone in advancing Proofpoint’s mission to deliver human-centric security solutions to businesses of all sizes across the globe.

Proofpoint Launches Next-Gen Digital Communications Governance Offering with Enhanced Capture, Archiving and Supervision Innovations.

Market-leading human-centric security solutions trusted by many of the largest companies in the Middle East to be available through local data center in Dubai.

Gartner evaluated 14 vendors for its 2024 report and recognised Proofpoint as a Leader for its Ability to Execute and Completeness of Vision.

Amid the region’s growing retail market, cybersecurity measures are critical to protecting shoppers against phishing, ransomware, and business email compromise threats.
GET TAHAWULTECH.COM IN YOUR INBOX