New integrated capability helps organisations detect advanced threats in backup data and restore with confidence. Cohesity, the leader in AI-powered …



New integrated capability helps organisations detect advanced threats in backup data and restore with confidence. Cohesity, the leader in AI-powered …

New CloudSEK research reveals how the APT group has evolved its tooling with a stealthy Rust implant to strengthen persistence, …
Attackers using highly convincing, animated lures to trick users into trusting malicious sites and downloads. Threat actors carrying out convincing campaigns with …

OPSWAT has released its first-ever Threat Landscape report, which shows that traditional detection methods are now being firmly outplaced, whilst …

Distributed via Skype and Telegram channels, GriffithRAT is typically disguised as files containing financial trend analysis or investment advice.

This innovative platform offers access to a continuously updated database of publicly available malware reports, allowing security professionals to gain critical insights into how malware behaves, evolves, and threatens organisations worldwide.
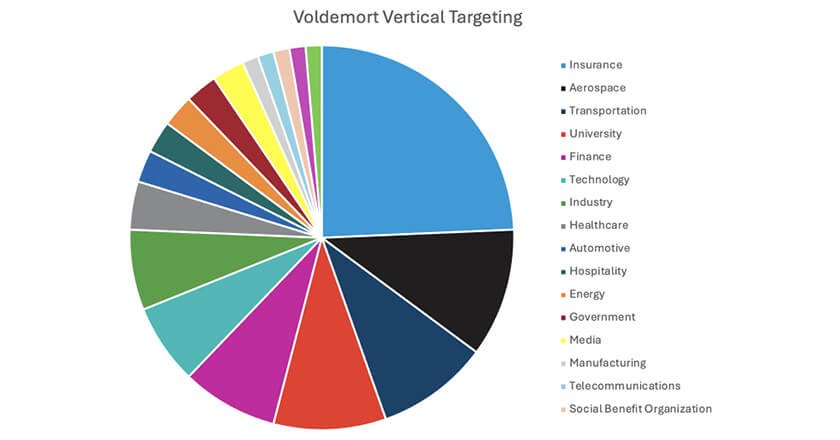
The malicious activity, first observed at the beginning of August 2024, included over 20,000 global messages impacting over 70 organizations.

Tahawultech.com spoke to cybersecurity industry frontrunners to learn more about the pitfalls of online shopping and tips to shop safely …

Steven Kenny, Architect & Engineering Program Manager EMEA at Axis Communications, writes an exclusive opinion piece for Tahawultech.com on how …
Proofpoint researchers identified a new malware call WikiLoader. It was first identified in December 2022 being delivered by TA544, an actor that typically uses Ursnif malware to target organisations.
GET TAHAWULTECH.COM IN YOUR INBOX