Google has credited Kaspersky for uncovering and reporting the issue, reflecting the company’s ongoing commitment to collaboration with the global cybersecurity community and ensuring user safety.
Google has credited Kaspersky for uncovering and reporting the issue, reflecting the company’s ongoing commitment to collaboration with the global cybersecurity community and ensuring user safety.

Prioritised remediations enhance security across endpoints, servers, Cloud and SaaS environments, reducing alert fatigue and enabling organisations to strengthen their defences before attacks occur.
ESET Research found an advertisement for a zero-day exploit that targets the Telegram for Android app, posted in an underground forum.

FortiGuard Labs’ 2H 2023 Global Threat Landscape Report highlights the need for vendors to adhere to vulnerability disclosure best practices …

Terry Young, Director of Service Provider Product Marketing, A10 Networks explores the most pressing attack vector for organisations to be aware of in the coming months.

Fady Younes, Cybersecurity Director, EMEA Service Providers and MEA, at Cisco, has penned an exclusive thought leadership article for tahawultech.com …

ChatGPT exploded into the public domain in November last year, and since then has continued to dominate column inches globally. …

(A10 Networks): Understanding and Preventing the Log4j Exploit and Botnets.

Sophos, a global leader in next-generation cybersecurity, has announced in the Sophos X-Ops report, “Cookie stealing: the new perimeter bypass,” …

Mandiant Reveals More Zero-Days Exploited in 2021 Than Ever Before.

ESET Threat Report: Attempts to exploit MS Exchange and massive waves of password guessing were the most frequent intrusion vectors.

How to get away with malware: top streaming platforms and shows exploited by cybercriminals discovered.

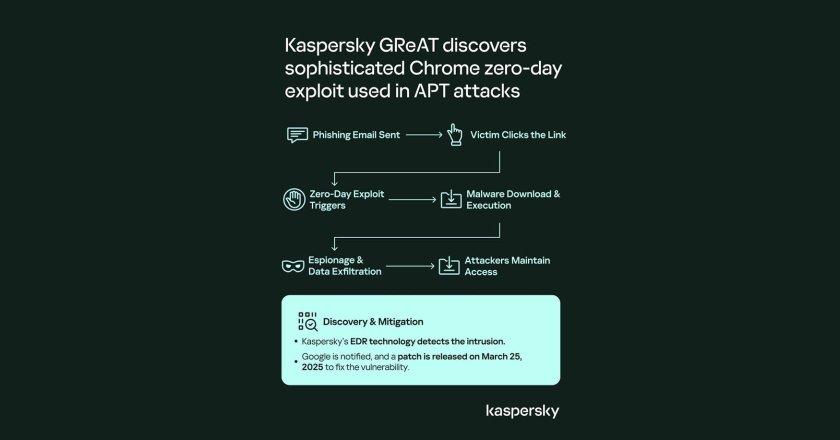
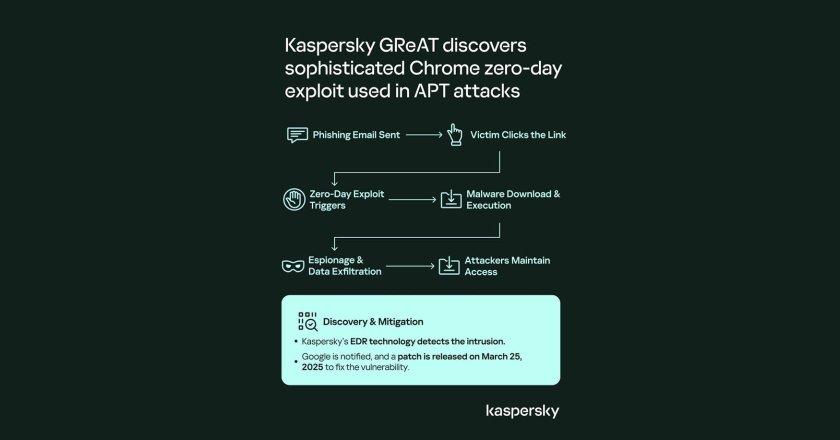
Advanced threat actors are continuously changing their tactics, sharpening their toolsets, and launching new waves of activity. That’s why, to keep users and organisations informed about the threats they face, Kaspersky’s Global Research and Analysis team provides quarterly reports about the most important developments in the advanced persistent threat landscape.

A new report published by Vectra examined how cybercriminals are using built-in Office 365 services in their attacks on enterprises.

Vectra AI has released its 2020 Spotlight Report on Healthcare, which shows an upward trend in exploitable behaviours and discredits claims that external threats would lead to increased internal threat activity.

Kaspersky Lab technologies have automatically detected a new exploited vulnerability in the Microsoft Windows OS kernel, the third consecutive zero-day exploit to be discovered in three months.

US president Donald Trump accused Amazon.com on Thursday of not paying sufficient tax, exploiting the US postal system and putting …

UAE-based on-demand IT services provider Geeks.ae has offered its top tips to prevent cybercriminals from exploiting user devices to mine …

The report claims that malicious uses of AI could lead to driverless car crashes, or result in commercial drones being converted into targeted weapons.

The UAE and India have signed an historic agreement that could stop unscrupulous local employers who fail to deliver on …