 Ransom attackers have finally made the jump from Windows to the Mac with news of a stunningly simple hack that tries to trick browser users into paying a $300 (£200) fine using a simple JavaScript routine.
Ransom attackers have finally made the jump from Windows to the Mac with news of a stunningly simple hack that tries to trick browser users into paying a $300 (£200) fine using a simple JavaScript routine.
The attack noticed by security firm Malwarebytes is a mixture of sleight of hand and social engineering that the firm reports that it will work against several Mac-based browsers (using an OSX interpreter) with JavaScript enabled.
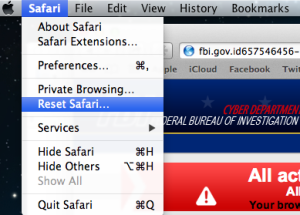
Victims reportedly encounter it after running one of a number common searches where they are unlucky enough to end up on the ransom attack page. This demands the money on behalf of the FBI for claimed copyright infringement or downloading porn.
It’s the common garden police ransom scam, made more implausible by its request to receive the money as a US GreenDot MoneyPak code of the sort that can be bought for cash from Walmart. The scammers even use a bogus FBI URL in an attempt to add a small element of authenticity.
The problem is that getting rid of the page appears to be impossible thanks to an embedded iFrame that fires up the page 150 times to deter the user; leaving or closing the page is impossible.
Attempting to ‘force quit’ Safari looks as if it has worked but reloading brings up the same page again and again. The only way out of the loop is to force reset the browser (which will lose some of its settings) or, less radically, by holding down the shift key to stop the same page reappearing.
Because the JavaScript is on the web page, there is no malware involved here. The same attack principle could be tried against Windows browsers too as long as JavaScript is enabled and it works with their interpreters.
PCs are usually assailed by more complex types of ransom malware. The attackers probably chose this method to wield against Macs because it involves no complex programming to speak of and Apple users are seen as easy meat. Ransom attacks are still in their infancy on the platform.
“Cyber-criminals, well known for not re-inventing the wheel, have ‘ported’ the latest ransomware to OS X, not by using some complicated exploit but rather leveraging the browser and its ‘restore from crash’ feature,” said Jerome Segura of Malwarebytes.
“The bad guys know how to use social engineering to entice victims as, for example, I was lead to this locked page by doing a search for Taylor Swift on Bing images.”
The attack’s surprise is its simplicity. Occasionally in cyber-crime, it is the simplest attacks that are the cleverest. This particular one isn’t complex but it might be good enough to catch at least some victims.