Digital Shadows has unveiled research into some of the main techniques cybercriminals are using to target organisations using stolen credentials which have been reused across a variety of sites and online forums.
The report titled, “Protect Your Customer and Employee Accounts: 7 Ways To Mitigate The Growing Risks Of Account Takeovers” also outlines what measures organisations can implement to protect against such attacks.
The research reveals that cybercriminals are increasingly turning to credential stuffing tools to automate attempts at account takeover. This is a type of brute force attack whereby large sets of credentials are automatically inserted into login pages until a match with an existing account is found. Based on configurations, the most common targets for these attacks are the gaming, technology, broadcasting and retail sectors.
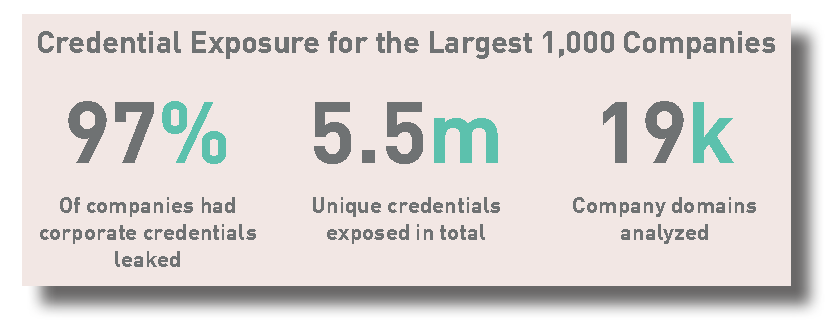
Last year, Digital Shadows found that 97 percent of businesses in the ‘Forbes 1000’ had their valuable credentials exposed, usually by employees using the same details across multiple sites and platforms. Now criminals are recognising that employees often have poor username and password discipline to use these in mass automated credential stuffing attacks aiming to gain access to corporate networks.
“Many organisations are suffering breach fatigue due to the huge numbers of credentials exposed via not only high profile incidents like those suffered by Myspace, LinkedIn and Dropbox, but also from tens of thousands of smaller breaches,” said Rick Holland, VP Strategy, Digital Shadows. “But it is critical that businesses arm themselves with the necessary intelligence and insight to manage their digital risk and prevent this problem credential exposure from escalating into an even more severe problem.”

The report also suggests that while multi-factor authentication (MFA) can help to protect organisations and their customers from account takeovers, it cannot be seen as a silver bullet to solve the problem of account take overs.
“Enterprises – and the companies that work for and with them – need to be better prepared for this sort of brute force attack,” added Holland.
Other steps businesses should take to protect against credential stuffing include:
- Monitor for leaked credentials of your employees. Troy Hunt’s https://www.haveibeenpwned.com is a great resource for this, alerting you to instances of breaches including your organisation’s email domain.
- Monitor for mentions of your company and brand names across cracking forums. This can help to inform the security solutions you invest in. Use Google Alerts for this – Johnny Long some great tips for doing so (http://www.mrjoeyjohnson.com/Google.Hacking.Filters.pdf) and it can help identify the specific risks to your business.
- Monitor for leaked credentials of your customers, allowing you to take a more proactive response.
- Deploy an inline Web Application Firewall. Commercial and open source web application firewalls, like ModSecurity, can be used to identify and block credential stuffing attacks.
- Increase user awareness. Educate your staff and consumers about the dangers of using corporate email address for personal accounts, as well as reusing passwords.
- Gain an awareness of credential stuffing tools. Keep an eye on the development of credential stuffing tools, and of how your security solutions compare to their capabilities.
- Implement multi-factor authentication that doesn’t leverage SMS. This can help to reduce account takeovers, but make sure this is balanced against the friction it can cause.
You can access the full report at: http://info.digitalshadows.com/AccountTakeover-PR_Registration.html





