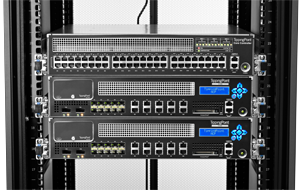
 HP announced last week that it plans to use its recently unveiled SDN controller to distribute its TippingPoint intrusion prevention system across networks. This will help to overcome the scale limitations of dedicated appliances, the firm said.
HP announced last week that it plans to use its recently unveiled SDN controller to distribute its TippingPoint intrusion prevention system across networks. This will help to overcome the scale limitations of dedicated appliances, the firm said.
The research project, called Sentinel, is one of HP’s first steps to use the distributed nature of SDN (software-defined networking) to change what networks can do. In this case, SDN can make it easier to provide protection against Internet malware throughout an enterprise or carrier network. Sentinel can scale up to handle thousands of endpoints, helping to keep enterprises secure as they embark on BYOD (bring your own device) policies, said Mauricio Sanchez, chief security architect at HP Networking.
“It’s bringing that level of capability to the entire network and not just to the Internet gateway,” Sanchez said. Leveraging its security capabilities along with SDN is one move by HP to compete with rivals such as Cisco and Juniper in the rapidly evolving SDN market.
TippingPoint keeps track of known sources of malware on the Internet, with a list of about 700,000 sites today, according to the company. It consists of software and an accompanying service, in which security researchers identify sites that contain hazardous code.
Currently, the TippingPoint software is deployed in appliances, which are installed as gateways between the public Internet and a private network. But those appliances can become bottlenecks because their performance is limited by the speed of their network links and hardware components.
Researchers at HP are now working on turning TippingPoint into an application that runs on HP’s SDN controller, said Sanchez, a co-creator of the application. Because SDN separates the control of a network from its forwarding plane, it allows networking applications to be distributed wherever in the network they need to be. HP’s controller is designed to host many different applications.
Sanchez demonstrated Sentinel at a media event on Thursday. The software works by capturing and analysing the DNS (Domain Name System) traffic that’s generated when a user on the network tries to go to a website. If the site’s DNS information matches that of any site on the TippingPoint list, Sentinel will take action over the network using the OpenFlow protocol, Sanchez said. It can redirect the user’s request or take other steps, including sending a warning that the endpoint may have gone to that site because it was infected.
Because the Sentinel application has a real-time connection to the TippingPoint service, which updates its database at least every two hours, it has the latest information to secure the network. And because it only captures DNS traffic instead of the full flow of Web-browsing data, it can work efficiently, Sanchez said.
HP is actively working on a commercial version of Sentinel and expects one to be available this year, Sanchez said. HBO is an early release customer, and the software is being prototyped and tested on that company’s network, he said. HP has also been talking to several telecommunications carriers about using Sentinel on their backbone networks, Sanchez said.
Sentinel is complementary to the current TippingPoint offering but its scalability is a key benefit to carriers and enterprises, according to HP.
“In order to get the kind of coverage and scale that you get with software-defined networking, what people would have to do today is deploy a lot of appliances throughout their network. And let’s face it, not many people are willing to do that unless they’re very, very paranoid,” Sanchez said.