Fortinet, a global cybersecurity leader driving the convergence of networking and security, has announced the general availability of Lacework FortiCNAPP, …
Fortinet, a global cybersecurity leader driving the convergence of networking and security, has announced the general availability of Lacework FortiCNAPP, …

CNME Editor Mark Forker spoke to Nader Paslar, General Manager at CODE81, the new player in the AI space that …

Tenable Introduces Tenable.cs to Provide Security from Code to Cloud.

The TOR Project is advising that people stop using Windows after the discovery of a startling vulnerability in Firefox that undermined the main advantages of the privacy-centered network.

A new report from Forrester Research says these “post-PC” devices could fill a niche, or more than one, in the enterprise.

Cisco is building a router for the Internet of Everything, the company’s initiative to connect the billions of devices – or 99 percent of the world – that it claims isn’t already connected.

Symantec has discovered a bizarre ransom Trojan that eschews the usual demand for payment in favour of asking its victims to fill in an online survey to get an unlock code.

In June, ABI Research made waves with a report that claimed Intel’s “Clover Trail” Atom chip consumed just 60 percent of the power of a competing ARM chip, with comparable performance. Now, another analyst has claimed that’s simply not true.

With the previously $40,000 Carberp Trojan’s source code now freely available, experts expect exceptionally destructive variants of the malware to flow onto the Internet.
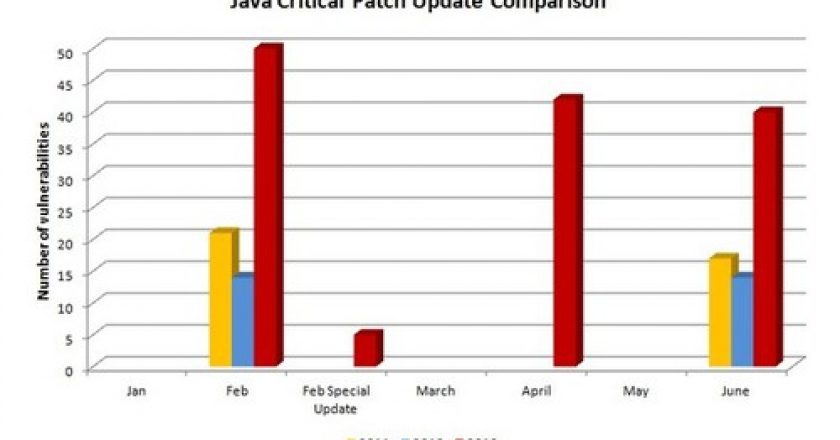
Oracle released a huge update for the virtually ubiquitous software, but attackers aren’t done exploiting Java as the weakest link in the security chain, and Oracle isn’t securing it fast enough.
GET TAHAWULTECH.COM IN YOUR INBOX