New innovations simplify data activation and resilience management through secure AI integration and natural language interaction Dubai — Commvault, a …



New innovations simplify data activation and resilience management through secure AI integration and natural language interaction Dubai — Commvault, a …

Kaspersky presented the results of a security audit that has exposed a significant security flaw enabling unauthorized access to all connected vehicles of one automotive manufacturer.

The group stands out for its strong command of Russian and knowledge of local nuances, traits that Kaspersky observed in other campaigns linked to this APT threat.
Cybercriminals are exploiting users’ interest in the new film, luring them with the promise of free access to the anime.

Helps organisations understand the why behind issues across private and public cloud environments. Dubai — NETSCOUT Systems Inc. (NASDAQ: NTCT), …

Survey: While most Dubai consumers trust organisations to protect their data, 44% would consider stopping doing business with an enterprise if a breach occurred.

Such behaviour can put children at risk by exposing their identity, location, and/or personal moments to strangers, who could potentially misuse this information.

US agents take down telecoms threat near UN summit.

Day of delays at Heathrow after cyber-attack brings disruption.
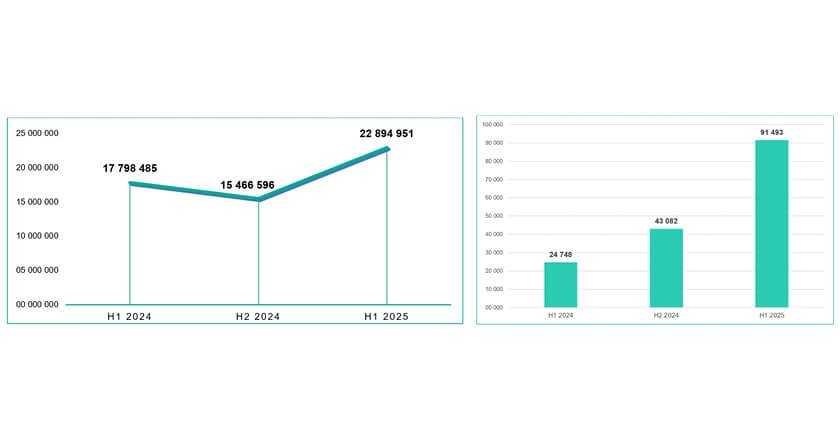
The number of mobile banking trojans detected in the first half of 2025 is almost four times more than in the first half of 2024 and over two times more than in the second half of 2024.