ESET Research has discovered a previously undetected China-aligned Advanced Persistent Threat (APT) group, PlushDaemon, engaged in cyberespionage operations.

ESET Research has discovered a previously undetected China-aligned Advanced Persistent Threat (APT) group, PlushDaemon, engaged in cyberespionage operations.

How edge devices are becoming hackers’ gateway into Industrial IoT.

Acronis, a global leader in cybersecurity and data protection, is pleased to announce the appointment of Gerald Beuchelt as its …
Geneva, Switzerland — The World Economic Forum’s Global Cybersecurity Outlook 2025 report released today highlights the increasing complexity in the cyber landscape, which has …

Dubai — The 26th edition of Intersec, the world’s biggest business event mapping the future of security, safety and fire …

Sophos MDR Grows Global Customers by 37% in 2024, Setting a Powerful New Standard in Cutting-edge, Expert-driven Cybersecurity Against Today’s Most Advanced Threats.

The UAE has consistently demonstrated leadership in innovation and possesses the ability to anticipate future trends impacting sustainable economic development. …

Exploring SentinelOne’s strategic adaptations and technological advancements in response to the dynamic cybersecurity market conditions of 2024. In 2024, SentinelOne …

Dubai — Cloud Box Technologies (CBT), a premier systems integrator and IT services specialist in the Middle East, has received …
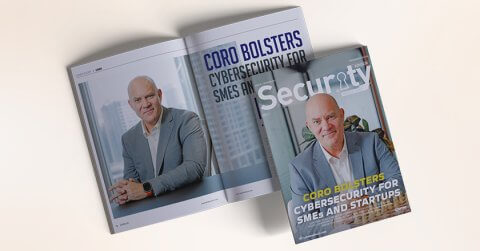
Exploring Coro’s proactive cybersecurity solutions in the dynamic digital landscape of the Middle East, with insights from Piers Morgan, Senior …