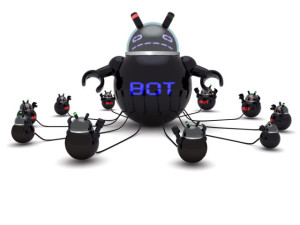
 Microsoft estimates that 88 percent of botnets running the Citadel financial malware were disrupted as a result of a takedown operation launched by the company in collaboration with the FBI and partners in technology and financial services. The operation was originally announced on June 5.
Microsoft estimates that 88 percent of botnets running the Citadel financial malware were disrupted as a result of a takedown operation launched by the company in collaboration with the FBI and partners in technology and financial services. The operation was originally announced on June 5.
Since then, almost 40 percent of Citadel-infected computers that were part of the targeted botnets have been cleaned, Richard Domingues Boscovich, an assistant general counsel with Microsoft’s Digital Crimes Unit, said Thursday in a blog post.
Microsoft did not immediately respond to an inquiry seeking information about how those computers were cleaned and the number of computers that remain infected with the malware.
However, Boscovich said in a different blog post on June 21 that Microsoft observed almost 1.3 million unique IP (Internet Protocol) addresses connecting to a “sinkhole” system put in place by the company to replace the Citadel command-and-control servers used by attackers.
After analyzing unique IP addresses and user-agent information sent by botnet clients when connecting to the sinkhole servers, the company estimated that more than 1.9 million computers were part of the targeted botnets, Boscovich said at the time, noting that multiple computers can connect through a single IP address.
He also said that Microsoft was working with other researchers and anti-malware organizations like the Shadowserver Foundation in order to support victim notification and remediation.
The Shadowserver Foundation is an organization that works with ISPs, as well as hosting and Domain Name System (DNS) providers to identify and mitigate botnet threats.
According to statistics released Thursday by Boscovich, the countries with the highest number of IP addresses corresponding to Citadel infections between June 2 and July 21 were: Germany with 15 percent of the total, Thailand with 13 percent, Italy with 10 percent, India with 9 percent and Australia and Poland with 6 percent each. Five percent of Citadel-infected IP addresses were located in the U.S.
Boscovich praised the collaboration between public and private sector organisations to disrupt the Citadel botnet.
“By combining our collective expertise and taking coordinated steps to dismantle the botnets, we have been able to significantly diminish Citadel’s operation, rescue victims from the threat, and make it more costly for the cyber-criminals to continue doing business,” he said Thursday in the blog post.
However, not everyone in the security research community was happy with how the take-down effort was implemented.
Shortly after the takedown, a security researcher who runs the abuse.ch botnet tracking services estimated that around 1,000 of approximately 4,000 Citadel-related domain names seized by Microsoft during the operation were already under the control of security researchers who were using them to monitor and gather information about the botnets.
Furthermore, he criticized Microsoft for sending configuration files to Citadel-infected computers that were connecting to its sinkhole servers, saying that this action implicitly modifies settings on those computers without their owners’ consent. “In most countries, this is violating local law,” he said in a blog post on June 7.
“Citadel blocked its victims’ ability to access many legitimate anti-virus and anti-malware sites in order to prevent them from being able to remove the malware from their computer,” Boscovich said on June 11 in an emailed statement. “In order for victims to clean their computers, the court order from the US District Court for the Western District of North Carolina allowed Microsoft to unblock these sites when computers from around the world checked into the command and control structure for Citadel which is hosted in the US.”