Manufacturers’ ability to run sustainable digital operations is threatened by continued use of legacy systems, according to IDC.


Manufacturers’ ability to run sustainable digital operations is threatened by continued use of legacy systems, according to IDC.

This Russian-speaking actor uses a wide variety of malware implants developed at a rapid pace and in all programming languages imaginable, presumably in order to obstruct attribution.

In the wake of Earth Day 2023, Kaspersky reveals new data on the environmental impact of blocking crypto miners.

The Most Common Root Causes of Attacks Were Unpatched Vulnerabilities and Compromised Credentials, While Ransomware Continues to Be the Most Common “End Game”.
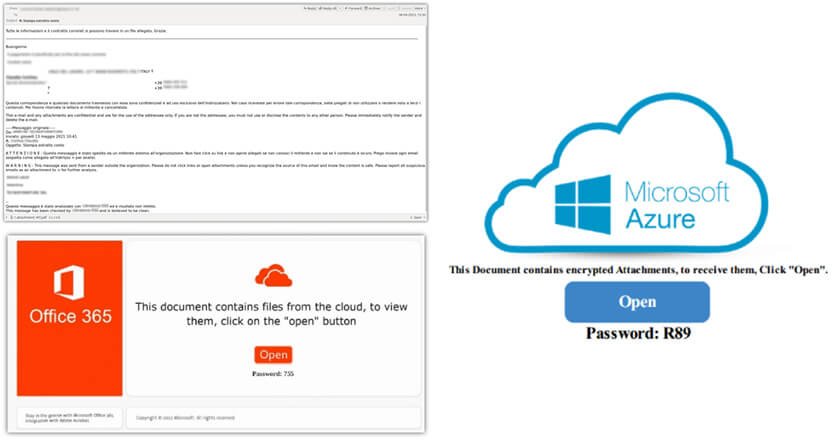
Kaspersky discovered a Qbot malware spike targeting corporate users, spread via a malicious spam-email campaign.

Sam Tayan, Head of METAP at Zoom explains how interpersonal interactions, workflows, and communication channels between workers, teams, and customers …

62% of businesses prefer a Unified AI- and ML-powered observability solution to provide a better customer experience.

Over 56% of the core routers ESET purchased from secondary market vendors contained a treasure trove of sensitive data, including corporate credentials, VPN details, cryptographic keys, and more.

Gaurav Mohan, VP, SAARC & Middle East, NETSCOUT highlights that to become an unstoppable enterprise, organizations must consider five essential …

Chady Smayra and Diana Dib, partners with Strategy & Middle East, part of the PwC network, discuss how the GCC …

Ramy Sfeir, Partner, Sami Darouni, senior executive advisor, Nitin Manoharan, executive advisor, and Makram Debbas, principal, with Strategy& Middle East, …

Search engine passes 100-million milestone for daily users following February’s launch of a range of advanced capabilities, from automated research summaries of large-text sources to help with text composition for social media posts.
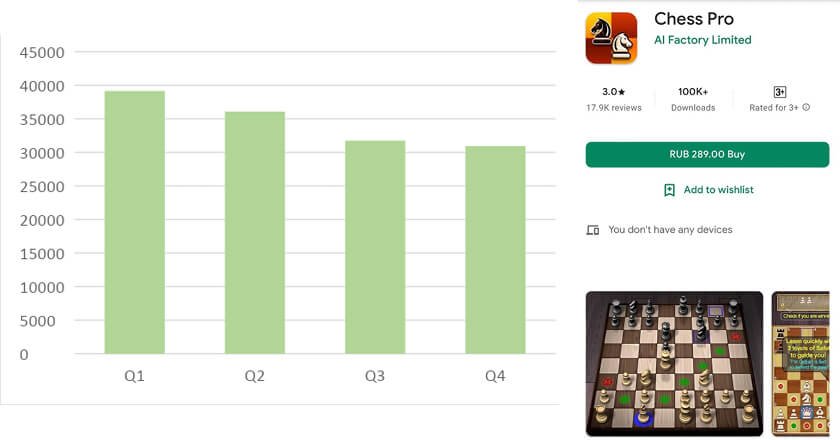
Kaspersky cybersecurity experts have discovered that chess players have been targeted by a range of different attacks from cybercriminals spreading malicious or unwanted mobile programs 一 even on Google Play 一 and Trojans and ransomware disguised as chess applications.

A cybercriminal group used an exploit developed for different versions and builds of Windows OS, including Windows 11, and attempted to deploy the Nokoyawa ransomware.