As per the agreement, the distributor will extend its portfolio of security solutions in the region.


As per the agreement, the distributor will extend its portfolio of security solutions in the region.
The final member of a Manchester-based phishing gang that stole £1.5 million ($2.5 million) from UK students by setting up a bogus facsimile of the UK Student Loans Company has been sentenced to three years and nine months in prison.

Reading the coverage of the recent breach of Adobe passwords, we learned that 1.9 million users used “123456” as their password. That’s right: out of 38 million cracked passwords, almost two million adults used ones more suited to five-year-olds.

Big Data is improving decision making, according to a newly released global survey by EMC.

Trend Micro has outlined its security predictions for 2014, and it has forecast that one major data breach will occur every month next year.

Hackers infiltrated computers belonging to the foreign affairs ministries of five unnamed European countries ahead of the G20 Summit in September, according to security researchers at FireEye.

New attack campaigns have infected point-of-sale (PoS) systems around the world with sophisticated malware designed to steal payment card and transaction data.

When it comes to security, it seems everyone’s in a state of perpetual panic. Whether it’s mobile malware, BYOD or hacktivism, over the course of 2013 the issue of protecting valuable information and resisting attack has inspired a dizzying and persistent challenge.

A new Trojan programme that targets users of online financial services has the potential to spread very quickly over the next few months, security researchers warn.

Because data is often the most valuable corporate asset – especially when customer information is concerned – staying alert for potential compromise is a critical IT job. Unfortunately, looking into a potential data breach is not easy.
A new malicious software programme, advertised for sale on underground forums, claims to mine and steal bitcoins, according to a …

Through the advent of mobility, smartphones and tablets are now more dangerous devices to enterprises than laptops and PCs.
Mobile malware continues to proliferate, and at the same time employees are insisting on bringing their personal devices to work.

The website of a U.S. organization specializing in national and international security policy was compromised with malware that targeted a previously unknown vulnerability in Internet Explorer.

Security researchers have uncovered two unpatched vulnerabilities in Internet Explorer (IE) which have been exploited by attackers in an unusual “watering hole” campaign launched from a U.S.-based website that specialises in domestic and international security policy.

New features include inline sandboxing defenses, malware isolation, phishing education and new platform support

“Collecting more and more unstructured data will open up another whole degree of attractiveness and may well lead to attackers seeing value in a form not previously recognised by the organisation that owns the data.”
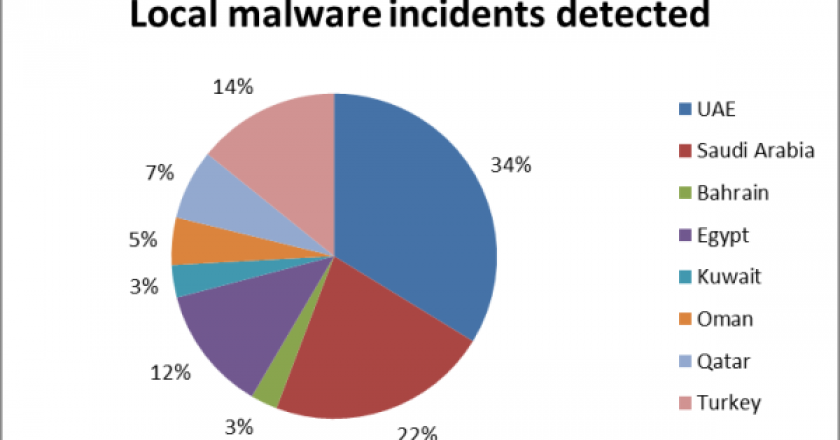
Kaspersky Lab has revealed research results that show an increase in malware in the Middle East.

Cyber Security@Crossroads roadshow enabled enterprises to address their security challenges.

The US National Security Agency has repeatedly tried to compromise Tor, the government-funded online anonymity tool, but has had little success, according to a new report in the UK’s Guardian.
With the addition of these services, Help AG strengthens its position