In a statement, Intel says that the new vulnerabilities discovered by Google do not have the power to corrupt, modify or delete data, and says it has started providing software and firmware updates to mitigate these exploits.
While acknowledging the security flaw (now referred to as a side channel analysis exploit), the CPU vendor says contrary to some reports, any performance impacts from the patches are workload-dependent, and, for the average computer user, should not be significant and will be mitigated over time.
The company has also denied recent reports that these exploits are unique to Intel products. Based on the analysis to date, many types of computing devices — with many different vendors’ processors and operating systems — are susceptible to these exploits, says Intel.
Intel adds that it is committed to product and customer security and is working closely with many other technology companies, including AMD, ARM Holdings and several operating system vendors, to develop an industry-wide approach to resolve this issue promptly and constructively.
Intel has urged users to check with their operating system vendor or system manufacturer and apply any available updates as soon as they are available. Following good security practices that protect against malware in general will also help protect against possible exploitation until updates can be applied, says the vendor in the statement.
What is a side-channel analysis exploit?
According to Intel, the exploit is a way for an attacker to observe the content of privileged memory, exploiting a CPU technique called speculative execution to circumvent expected privilege levels. That can give an attacker access to data it normally wouldn’t, though Intel has said that the data won’t be deleted or modified.
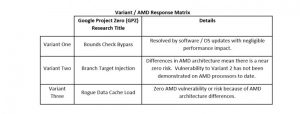
In fact, Intel and the researchers identified three variants, known as a “bounds check bypass,” “branch target injection,” and a “rogue data load,” all of which used slightly different methods of attack. In each case, operating-system updates mitigated the problem.
Steve Smith, one of the engineering leads at Intel who reported the company’s findings, added that no attacks using the vulnerability has been discovered in the wild. He also denied reports that the vulnerability was a flaw, or that it was specific to Intel. “The processor is in fact operating as we designed it,” Smith told investors during the conference call.
The discovery led to hardware makers around the world responding to the vulnerability in a “responsible manner,” Smith said.
For its part, AMD denied that its processors were affected, stating that there was a “near zero risk to AMD processors” at this time. The company also outlined its responses to the three variants of the vulnerability in a graphic.
Google also reported that its Chrome browser is affected, though there’s a two-step cure: first, make sure that your browser is updated up to version 63. Second, an optional feature called Site Isolation can be enabled to provide mitigation by isolating websites into separate address spaces. This optional flag, which can be turned on at chrome://flags/#enable-site-per-process, turns on Site Isolation. Finally, Chrome 64, which will be released on Jan. 23, will protect users against the side-channel exploit, Google said.
(With additional reporting by Mark Hachman, PCWorld)