By adopting a comprehensive cybersecurity strategy, financial institutions can effectively protect their systems, safeguard sensitive customer data, and maintain their …


By adopting a comprehensive cybersecurity strategy, financial institutions can effectively protect their systems, safeguard sensitive customer data, and maintain their …

After an encouraging decline in 2022, the ransomware landscape saw a major escalation in the frequency, scope, and volume of …

Dave Russell, Vice President, Enterprise Strategy at Veeam explores how zero trust security processes have evolved in recent years and how in a landscape where the benchmark for security is constantly shifting, zero trust must continue to adapt in order to survive.

Anita Joseph caught up with Refat Al-Karmi, Senior Consultant, META at Juniper Networks, to find out more about its recently …

James Harvey, CTO Advisor EMEA at Cisco Observability, discusses how brands need to understand that consumers’ expectations of the total …
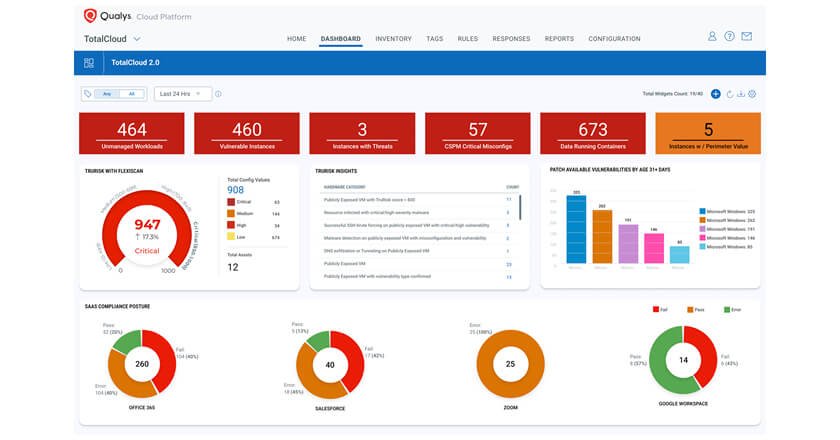
Expanded solution brings cloud infrastructure, SaaS apps and externally exposed assets together for a unified view of risk across multi-cloud environments.

Ericsson committed to reduce absolute scope 1, 2 and 3 greenhouse gas emissions by 90 percent between 2020 levels and the end of 2040.

Every day is Safer Internet Day. With data being the soul of businesses as well as virtual and vulnerable, it …

The campaign leveraged Google Play to distribute six malicious apps bundled with VajraSpy RAT code; six more were distributed in the wild.

Championing Privacy-First Security: Harmonizing Privacy and Security Compliance.

Yealink has thanked Positive Technologies for discovering the critical vulnerability BDU:2024-00482 in its Yealink Meeting Server videoconferencing system.

In an era dominated by digital interactions, Data Privacy Day serves as a stark reminder of the vital need to …

These training events reiterate Saudi Arabia’s commitment to advanced cybersecurity and nurturing the skills essential for safeguarding its digital future. …

The Women in Technology Forum and Awards stands out as a pioneering event in the region, dedicated to celebrating and honoring …

Anita Joseph caught up with Wesley Wang, Director of Channel Development & MarCom at Hikvision MEA to learn about the …

Organisers of LEAP 2024, the seismic technology event conceived to accelerate the adoption of technology and aid the ongoing transformation …

Anita Joseph caught up with Samer Mohamad, Yasmina Regional Director for MENA at Yango, the global technology company that recently …

PwC Middle East, one of the world’s leading professional services firms, is adding a further 1,000 roles over the next …

Cloudflare has announced its 2023 Q4 DDoS report – which showed that DDoS attacks reached new heights in 2023. This …

OPSWAT opened its Dubai offices in October last year to address the increasing demand across the region for zero-trust cybersecurity solutions capable of safeguarding critical infrastructure.