Play it safe: 5 reasons not to download pirated games.


Play it safe: 5 reasons not to download pirated games.

Create a Data Fortress for Protection against Ransomware Attacks.

Social Media Threat Awareness: Extend Security Awareness Skills to Personal Life.

1 in 5 HTML Email Attachments Found to be Malicious, Barracuda Research.

Acronis Signs Mindware as Cloud Distributor for GCC, Levant and Pakistan to Advance Cyber Protection for Regional Enterprises.

June 30th 2022: Acronis announced today its partnership with Mindware, one of the leading Value Added Distributors (VADs) in the …

Lookout Builds Momentum With Continued Strong Results.
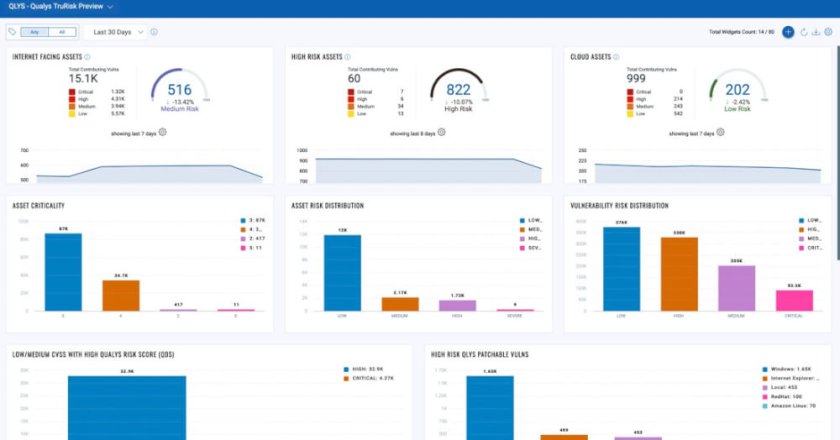
Qualys Launches VMDR 2.0 with TruRisk Scores and Automated Remediation Workflows.

Infoblox’s State of Security Report Spotlights Remote Work Hazards in the UAE.

Veeam Software. Building Trust in a Zero Trust Environment.

A10 Networks’ Threat Research Detects and Tracks Origins of DDoS Weapons; Observes Over 15 Million Weapons.
Cybersecurity Mitigations No Organisation Can Afford to Ignore.

Individuals found to be the top attack sector for cybercriminals – New research from Trellix.

Sophos Unveils Powerful Cloud Workload Protection Advancements with New Linux and Container Security Offerings.

Sophos Achieves Perfect Scores in SE Labs’ Protection Tests.

ESET Research: Ukraine hit by destructive attacks before and during the Russian invasion with HermeticWiper and IsaacWiper.

Vectra AI announces slate of free cybersecurity tools in response to expanding Ukraine-Russia conflict.

Email-Based Attacks Dominated the Threat Landscape in 2021.

ESET Threat Report: Attempts to exploit MS Exchange and massive waves of password guessing were the most frequent intrusion vectors.

Cybercriminals use new tactics to attack industrial organisations – all in a hunt for corporate credentials.