Cloudflare Democratises Spoof-Proof Security; Makes Hardware Security Keys More Accessible Than Ever for Millions of Customers Because it’s Good for the Internet.


Cloudflare Democratises Spoof-Proof Security; Makes Hardware Security Keys More Accessible Than Ever for Millions of Customers Because it’s Good for the Internet.
5 reasons to keep your software and devices up to date.

Veritas Introduces Veritas Alta: The Industry’s Most Comprehensive Cloud Data Management Platform.

Veronica Martin caught up with JS Wong, CEO at SendQuick to discuss GITEX 2022 and the company’s plans for the region.

By Sebastien Pavie, VP Data Protection Products, Southern EMEA at THALES Hardly a day passes without hearing of a new …

By Sebastien Pavie, VP Data Protection Products, Southern EMEA at THALES Key management – the processing, management and storage of …

Sebastien Pavie, Thales, dives into the cyber threat landscape and how employees can better prepare themselves for the onslaught from hackers.

Amir Kanaan, Managing Director for the Middle East Turkey and Africa at Kaspersky outlines how their operations have evolved, the impact of threat intelligence and the importance of SOCs.

Evren Aker, Director of Partnerships, Genesys, META and France outlines the issues frequently encountered with cloud transformation as well as the ‘decade of disruption’.

Amir Kanaan, Managing Director for the Middle East, Turkey and Africa at Kaspersky tells Anita Joseph why Threat Intelligence is essential …

ServiceNow Unveils the Now Platform “Tokyo” Release to Help Organisations Drive Business Transformation Amid Complex Macro Environment.

Smishing has been identified as a new and sophisticated method of obtaining personal and financial information from victims by using …

How Explainable Artificial Intelligence Can Propel the Growth of Industry 4.0.

Proofpoint research reveals 79% of top Saudi companies are putting customers at risk of receiving fraudulent emails.

Smishing vs. Phishing: Understanding the Differences.

Alteryx, Data combined with analytics is power for all.

Tenable Research has discovered that the Jumpstart environments for Microsoft’s Azure Arc do not properly use logging utilities common amongst …

Cash App fraud: 10 common scams to watch out for.
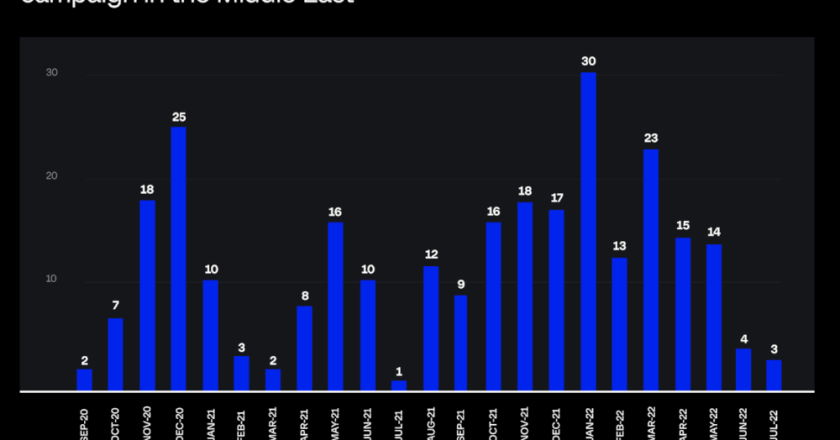
Over 200 Domains Impersonating Middle Eastern Postal Services: Group-IB Report.

Veeam: A Good Security Strategy Against Ransomware is at the Heart of Digital Transformation.