The Telecommunications Regulatory Authority (TRA) has launched the “UAE National Cybersecurity Strategy.”



The Telecommunications Regulatory Authority (TRA) has launched the “UAE National Cybersecurity Strategy.”
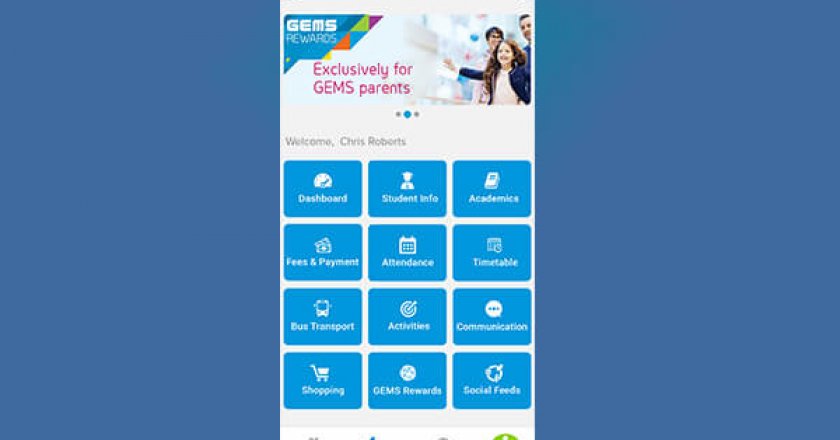
GEMS Education has launched a new app aimed at addressing the needs of the parents of existing as well as potential students.

UAE Minister of Economy Sultan bin Saeed Al Mansoori has issued a ministerial decision approving the upcoming acquisition of Careem by global firm Uber.

TÜV Rheinland’s regional manager for Asia Pacific, India, Middle East and Africa – Digital Transformation and Cybersecurity, John Ramesh shares insights into the evolution of the industrial sector and why security transformation within the space is now more important than ever.

Paul Hardy, chief innovation officer, ServiceNow, explains how customers and partners can help build new digital workflows and data models to impact business growth and profit positively.

UAE organisations rapidly investing in hybrid cloud environments will drive the country’s cloud business revenue to increase by $5.44 billion (AED 20 billion) to 2022.

People remain the greatest threat to industrial control systems (ICS) and associated networks, according to a new SANS survey.

UAE IT decision-makers agree that the public cloud is “important” for integrating future technology to transform citizen and customer experiences.

Huawei Middle East managin director and vice president of Enterprise Business Group, Alaa Elshimy gives his take on the future of WLAN technology with the advent of Wi-Fi 6.

ESET researchers have discovered fake cryptocurrency apps using a previously unseen technique to bypass SMS-based two-factor authentication (2FA), circumventing Google’s recent SMS permissions restrictions.
GET TAHAWULTECH.COM IN YOUR INBOX