Kingston Announces Hardware-Encrypted IronKey Keypad 200 USB Drive.
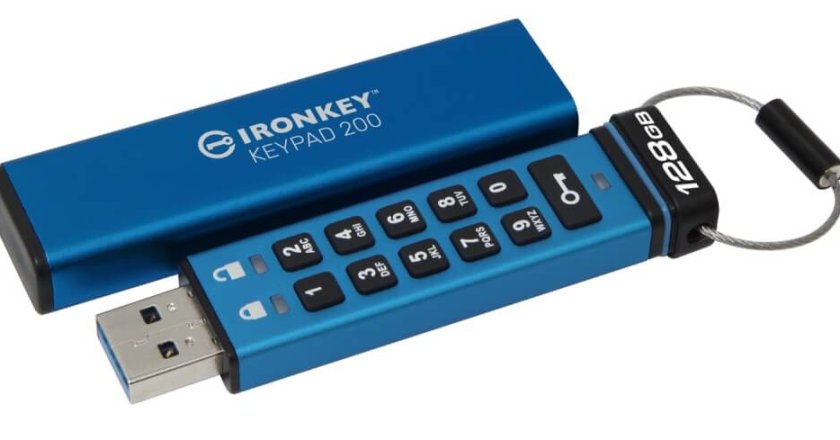
Kingston Announces Hardware-Encrypted IronKey Keypad 200 USB Drive.

(A10 Networks): Understanding and Preventing the Log4j Exploit and Botnets.

Smishing has been identified as a new and sophisticated method of obtaining personal and financial information from victims by using …

TikShock: Don’t get caught out by these 5 TikTok scams.

What is Good Cloud Migration Security?

ESET Research jointly presents Industroyer2 at Black Hat USA with Ukrainian government representative.

Cisco Experts Share Key Tips to Maintain Security in the Hybrid Work Environment.

Smishing vs. Phishing: Understanding the Differences.

Maher Jadallah, Senior Director Middle East & North Africa at Tenable Botnets first gained widespread notoriety in the early 2000s …

Mohamed Sabra, SMB Lead, Middle East and Africa at Cisco, tells Anita Joseph how small & medium-sized businesses can successfully navigate the nuances of hybrid work.

Kaspersky and Microsoft partner to deliver Threat Intelligence to Microsoft Sentinel users.

Sophos, a global leader in next-generation cybersecurity, has announced in the Sophos X-Ops report, “Cookie stealing: the new perimeter bypass,” …

Acronis, a global leader in cyber protection, unveiled its mid-year cyberthreats report, and the results of the report are worrying …

Threat Report – FortiGuard Labs Reports Ransomware Variants Almost Double in Six Months.

Staying safe online: How to browse the web securely.

The latest OT/IoT security report from Nozomi Networks Labs finds wiper malware, IoT botnet activity, and the Russia/Ukraine war impacted …
By Dan Woods, Global Head of Intelligence at F5 In the past two years, the world has been shocked economically, …

Cisco Reveals Top Cybersecurity Threats Trends in Q2 2022: Commodity malware on the rise surpassing ransomware.

The Evolving Cyber Threat Landscape and the Benefits of AI and Machine Learning.

‘Teen’ extortion-only group, LAPSUS$, exposes cyber gaps in the most mature organisations.