The Evolution of Work from Home – how IT holds the key to hybrid working models.


The Evolution of Work from Home – how IT holds the key to hybrid working models.

Global Lockdowns May Limit COVID-19, But Not DDoS.

FIN12: The Prolific Ransomware Intrusion Threat Actor That Has Aggressively Pursued Healthcare Targets.

53% of companies are left exposed to supply chain attacks, Acronis Cyber Readiness Report 2021 reveals critical security gaps.

Nozomi Networks Raises the Bar on Delivering Prioritised Actionable Intelligence for OT/IoT Networks to Accelerate Responses to Security Threats.

Multifactor authentication matters: 46% more users in UAE attacked with password stealers in 2021.

REvil has re-branded and committed to spare critical infrastructure from its attacks, but will this be enough to set back the rising tide of government action against ransomware hackers?

Etisalat has announced a new partnership with Microsoft to enhance the security of the UAE’s digital border and infrastructure.

Jose Menacherry of Bulwark Technologies talks with Nitya Ravi of CPI about their various security offerings.

As the industrial world becomes ever more connected and complex, the need to embed pervasive cybersecurity policies is paramount, says Tim Grieveson, Chief Information Security Officer, AVEVA.

What is RaaS and what does that mean? Ransomware as a Service (RaaS) means that you can simply purchase a service online, on the Dark Web, and you can then take whoever you want hostage at will. So, if you want to get rich quickly, all you need is a connection to the dark web, a credit card or other way to pay, and reprehensible morals.

Tips to Protect Enterprise Networks and Resources Against Mozi.

AHAD to Showcase Intelligence-Driven Visibility Solutions and Services at the GITEX Technology Week.
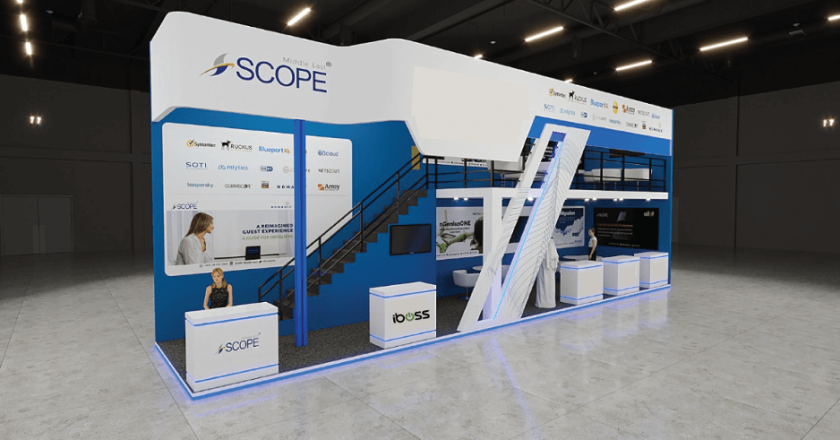
SASE Leader iboss to showcase at GITEX 2021.

FinFisher spyware improves its arsenal with four levels of obfuscation, UEFI infection and more.

5 Traits of a Great Endpoint Security System.

Maintaining an effective cybersecurity program can often be a challenging undertaking for any organisation. It also puts immense pressure on security leaders.

UAE: Industrial control systems spyware and malicious scripts on the rise in H1 2021.

Phishing Attacks on the Rise: 60% of Organisations in the UAE Report Increased Attacks During the Pandemic, According to Sophos Research.

Acronis rebrands its flagship personal cyber protection solution as Acronis Cyber Protect Home Office. The award-winning product (formerly Acronis True Image) provides individuals with comprehensive protection against all threats — from disk failures to cyberattacks.