A group that published hacking tools that security experts believe were stolen from the U.S. National Security Agency said on …


A group that published hacking tools that security experts believe were stolen from the U.S. National Security Agency said on …
A group of hackers that previously leaked alleged U.S. National Security Agency exploits claims to have even more attack tools …

Files released by the hacker group Shadow Brokers suggest the United States National Security Agency penetrated the SWIFT banking network …

Microsoft said it has already patched vulnerabilities revealed in Friday’s high-profile leak of suspected U.S. National Security Agency spying tools, …

Digital Shadows has announced new enhancements to its SearchLight digital risk management service helping organisations detect and respond to mobile application threats against their employees and consumers.
Digital Shadows has announced that it was named one of the world’s most innovative cybersecurity technologies of 2016 in the annual SINET 16 awards.

Digital Shadows has announced that it was named one of the world’s most innovative cybersecurity technologies of 2016 in the annual SINET 16 awards.

Under the terms of the agreement, Gulf Shadows will take on the Fujitsu client computing products which include notebooks, desktops, all-in-ones, tablets and displays for UAE.

Online Editor James Dartnell says shadow IT is something CIOs should use to their advantage, and should not be feared.

IT departments are “significantly underestimating” the budgets allocated to technology in others parts of the organisation, as more business leaders bypass the CIO and IT staff to execute their own projects, according to research.

The distributor will promote the manufacturer’s range of graphic cards.

The tech sector appears to be going about business as usual in the face of the US federal government shutdown, but some industry insiders are nervous about a long-term stoppage.

Symantec has discovered a bizarre ransom Trojan that eschews the usual demand for payment in favour of asking its victims to fill in an online survey to get an unlock code.

Hewlett-Packard CEO Leo Apotheker took a step out of Mark Hurd’s shadow yesterday, unveiling a new cloud computing platform that …
Jyoti Lalchandani, IDC’s Group Vice President and Regional Managing Director for the Middle East, Africa, and Turkey, discusses the Achilles heel that is shadow IT, and how IT arms can rein in the potentially damaging practice to benefit their business.

Once upon a time within Dell, managers who needed a business analysis report had to put in an IT request, a drawn out process that drove business units to set up their own shadow IT systems to run these numbers instead.
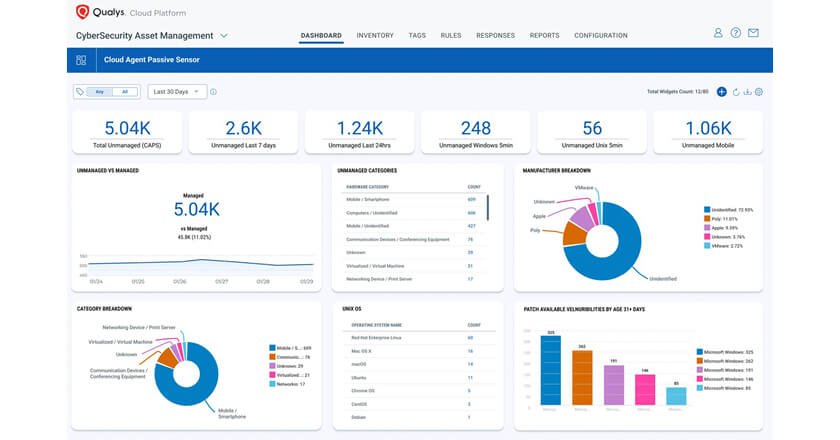
Groundbreaking functionality enables millions of cloud agents to discover risky unmanaged devices in real time with one click.

Low-code development’s potential to add value up and down the value chain, across departments, and all at every rung of the enterprise is clear.

Kaspersky Endpoint Security Cloud Pro’s features include root-cause analysis, cloud discovery and blocking, data discovery and integrated cybersecurity training for IT administrators.

Vectra opinion article for Tahawul Tech: how Attack Signal Intelligence can stop cybersecurity talent drain.