ESET has recently launched its latest consumer security product portfolio for Windows. The new range is designed to protect against …



ESET has recently launched its latest consumer security product portfolio for Windows. The new range is designed to protect against …
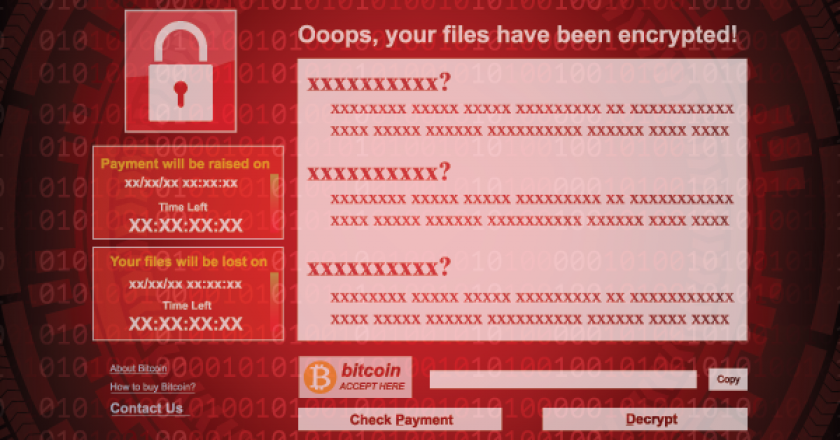
“After careful investigations, the United states is publicly attributing the massive WannaCry cyber-attack to North Korea,” said White House homeland security adviser Tom Bossert.
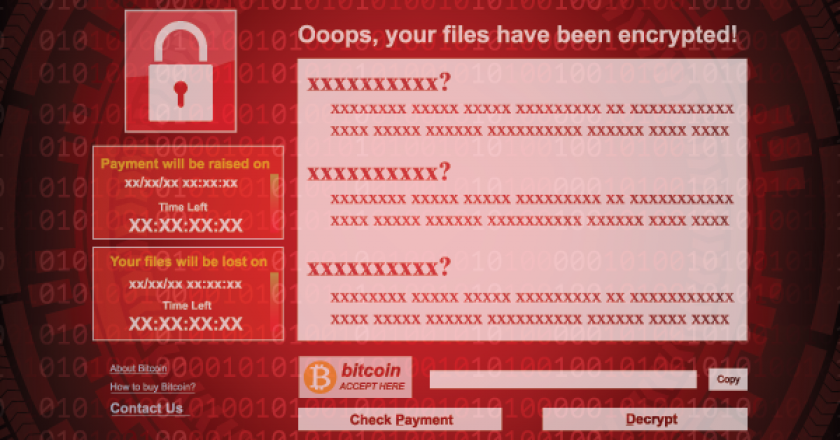
“The attack was widespread and cost billions, and North Korea is directly responsible,” wrote Homeland Security adviser to President Donald Trump Tom Bossert.

Lockheed Martin’s cyber kill chain approach breaks down each stage of a malware attack where you can identify and stop it.

Trend Micro, a global player in cybersecurity solutions, predicts the trend of known vulnerabilities being used in major attacks will …

Morey Haber, vice president of technology, BeyondTrust, lays out a set of critical factors that Middle East organisations should consider when building security awareness training programmes.

The number of IP-enabled IoT devices has increased dramatically in the last several years and according to Gartner, it is predicted …

Fortinet has unveiled predictions from the Fortinet FortiGuard Labs global research team about the threat landscape for 2018.

As AI tech transform modern IT systems, how can organisations leverage them to build better defences and stay on top of cybersecurity incidents?

The ransomware prompts users to download an Adobe Flash update when visiting an infected website instead of attacking a weakness in the computer’s security.
GET TAHAWULTECH.COM IN YOUR INBOX