On a recent trip to Dubai, Kaspersky Lab’s CEO and Founder Eugene Kaspersky took time out to tell James Dartnell about his greatest cybersecurity concerns for 2016, and the prospects for better threat defence in the enterprise and consumer spaces.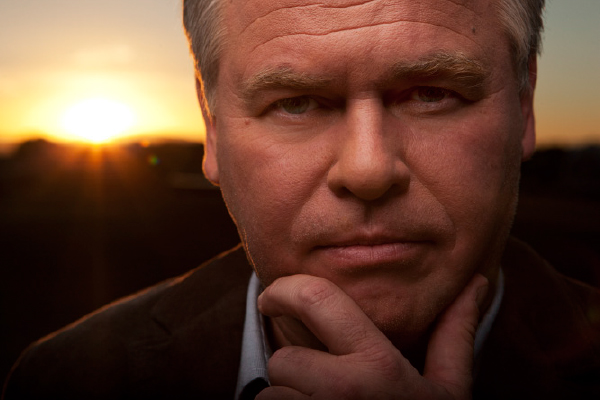
What does 2016 hold for cybersecurity and international threats?
The reality is that the threat of cyber-sabotage – attacks on critical infrastructure – is on our doorstep. From time to time there are incidents that are close to cyber-terrorism, but still don’t fall under the definition of terrorism. The attack on Aramco in 2012 is a prime example.
Another example is the failed attack on South Korean financial services. In 2007 there was an attack on Estonia, which resulted in an Internet blackout for the country. In Germany, an unspecificed attack on a steel mill which resulted in physical damage. Luckily, we don‘t have too many incidents like this, but I’m afraid more are coming. Attacks on physical, critical infrastructure is the worst case scenario.
Secondly, more and more professional cybercriminals are developing sophisticated technologies to attack well protected networks, and they are only getting more and more professional. They’re attacking banks, stock exchanges, high-powered targets. These criminal gangs are available as mercenaries; crime-as-a-service.
The next level of threats is the Internet of Things. What is the next device to be attacked? I think smart TVs will be vulnerable. Smart TV payments are on the rise, which is logical if I have a remote control and a big red ‘buy now’ button. In China, one company gives smart TVs away for free, with all channels connected to one provider. That’s surely a prime target for this type of threat.
In terms of mobile malware, are the Middle East and world at large aware of the risks?
It’s a global problem for most people, but one that is faraway. Until something really damaging happens, people’s awareness levels will not increase. We do our best to spread knowledge of attacks and risks in the space but there’s still a lot of work to do. It’s the same situation that existed with computer security 20 years ago – MS-DOS and Microsoft viruses existed but were not given attention. People just said “I’ll disinfect my PC.” In 1998, then in 1999, there were two global outbreaks of the ‘Chernobyl’ virus, which erased memory chips on motherboards. Desktops could be rescued, but notebooks were a problem as you could not remove the chip. The virus damaged the hardware, and it was more expensive to repair it than buy a new notebook. Over 300,000 were infected worldwide, and this was a big bang. This was a turning point. Awareness back then was relatively low. It’s the same now with mobile. I expect a mobile disaster. Mobile phones are everywhere. Before 2011, there were hundreds of attacks on smartphones per year. By 2012, there were tens of thousands, which is no coincidence as in 2011, many banks introduced mobile payments. The same big bang effect is still yet to take place with mobility.
With that being said, is the UAE a prime target for this type of threat?
I wouldn’t say that one country is more attractive than another. Countries with developed economies, major financial services and high mobile penetration rates are all facing problems. Criminals follow money. The Middle East is undoubtedly an attractive target.
Can you foresee a time where IT security teams have a perceived advantage against cyber-threats, and how far away is that point? What needs to be done to reach that stage?
It’s an arms race. We’re developing better technologies to defend, they’re developing ones for attack. It’s an endless fight. Technically it’s possible to create systems and applications that are immune to attacks. We are working towards that. Traditional cybersecurity is layered with the OS, applications and security on top of that. The concept of a secure OS is different, where security is in the middle of the OS, watching the application’s behaviour, so we can guarantee that all companies work in trusted scenarios, so that it’s not possible to infect the system. The problem is that developing this OS and its applications is expensive, and unfortunately, I don’t see a space for this technology in the consumer market. In that market, you need to deliver products as quickly as possible. Price matters. The product must be fast and cheap, and a secure OS is not about that. It’s slower to develop and more expensive. In an industrial environment, it’s the right time to introduce such secure platforms. It’s endless but will take time.
Are there any signs that archaic architectures could be rewritten in the coming years?
One of the biggest problems surrounding these architectures is that the engineers who designed and know how to operate them are retiring! Take Orly Airport in Paris. It ground to a halt last year because the weather controlling system – which operates on Windows 3.1 – stopped working. Two years ago, there was a call from a Canadian nuclear agency looking for PDP-11 – which was designed in the 1970s – engineers. A Norwegian oil firm has a device in the seabed which they said had to work for 30 years, without upgrades. Updating it means it needs to be taken up to the ship, changed and replaced at a cost of €3m, which is more expensive than the box itself. Many systems work like this. No nation in the world has enough resources to redesign these architectures and systems. I believe redesigning old architectures is a waste of time, and that we need to add new security layers to old systems.
Given these constraints, how can CIOs at an enterprise level get the best from their budgets?
The best thing for security officers to do is to learn more about the scenarios which can be used to attack their enterprises – their office and industrial networks. They should virtually design scenarios, and contact security companies and experts. We want to help CISOs understand their worst case scenarios, and help them explain to their board or upper management about the needs of IT security. The concept of cybersecurity has changed drastically in 10 years so now CISOs need to do more, and communicate what is needed to the board.
Is cybersecurity being taken seriously as a board-level issue?
Five years ago it wasn’t. A couple of years ago, I was at the World Economic Forum, where oil and gas CEOs were discussing it. They agreed that it was a top priority. Now, I think everyone is talking about it. We’re in touch with different companies in different industries and countries and they’re all considering it at this level.





