New research finds a new levelling of physical and cyber battlefields, revealing a thin line between physical war and cyber (through hacktivism)


New research finds a new levelling of physical and cyber battlefields, revealing a thin line between physical war and cyber (through hacktivism)

Attacks on Middle Eastern government agencies are mainly carried out by APT groups (56%), covertly establishing themselves in the victim’s infrastructure for the purpose of cyberespionage.

Scaled ransomware attacks against manufacturing and geopolitical tensions brought increased attention to the industrial cyber threat landscape.

Galaxy’s threat research team provides insights into the business impact of global threats.

Individuals found to be the top attack sector for cybercriminals – New research from Trellix.

Mandiant M-Trends 2022 Report Provides Inside Look at the Evolving Global Cyber Threat Landscape Directly from the Frontlines.

Cybereason reveals 2022 industry predictions for GCC stakeholders.

Mandiant Shares Top 14 Cyber Predictions for 2022 and Beyond.

Group-IB hosts “CyberCrimeCon 2021” to reduce the global impact of cybercrime.

A Look Ahead to 2022: McAfee Enterprise & FireEye Predict Top Cyber Threats.

Ibrahim Azab, regional sales director, MEA, Cyber Res, tells Security Advisor how the cybersecurity landscape is changing and what organisations must do to streamline …

In addition to the direct effects of the COVID-19 pandemic, we also saw a sharp rise in cybercriminal activity. From simple phishing attacks to one of the largest DDoS attacks ever recorded, we saw the cyber threat landscape evolve and grow. At the same time, we also saw a rapid growth in the tech and cyber security industry.

That’s why, this year, in addition to the usual global KSB reports, Kaspersky is offering a series of local predictions to ensure that, wherever you live, you can bring on a more secure 2021.

Cybereason Uncovers New Malware Arsenal Abusing Facebook and Dropbox in Middle East Espionage Campaign

Digitisation and advancements in information and communication technology have revolutionised every aspect of modern life. While a connected digital ecosystem …

Almost a third (30 percent) of cyber-attacks investigated by the Kaspersky Global Emergency Response team in 2019 involved legitimate remote management and administration tools.

FireEye has released the FireEye® Mandiant® M-Trends® 2020 report. The report shares statistics and insights gleaned from FireEye Mandiant investigations around the globe in 2019.

Trend Micro Incorporated, a global leader in cybersecurity solutions, has announced the findings of new research on the cyber risks …

Huawei Middle East’s president Charles Yang gives his take on building safer networks and securing the path to an intelligent world.
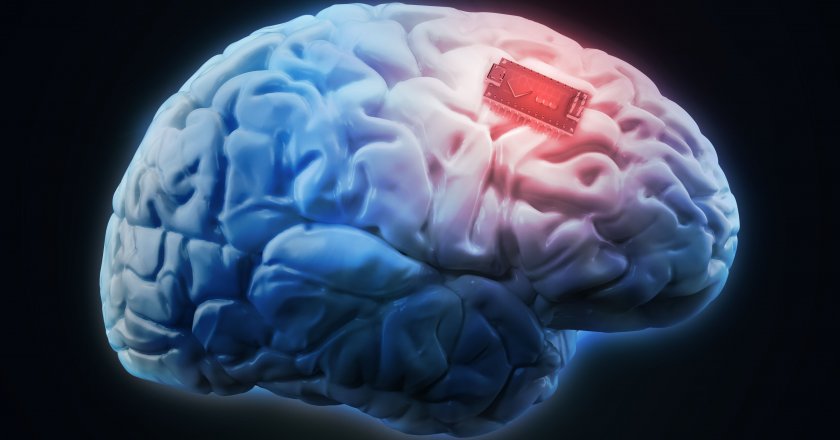
In the future, cyber-attackers may be able to exploit memory implants to steal, spy on, alter or control human memories. …