Trellix Advanced Research Centre’s investigation exposes serious vulnerabilities in CyberPower’s DCIM platform and Dataprobe’s iBoot PDU, highlighting potential unauthorized access …


Trellix Advanced Research Centre’s investigation exposes serious vulnerabilities in CyberPower’s DCIM platform and Dataprobe’s iBoot PDU, highlighting potential unauthorized access …

OPINION: Tarek Naja, Solutions Architect, at Qualys, believes that in order to overcome the complexities that come with moving workloads …
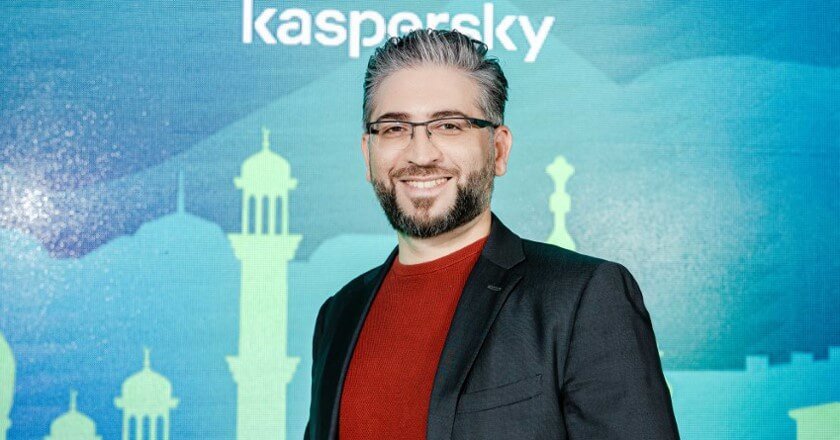
Kaspersky researchers announced the discovery of a series of attacks by a new malware supposedly developed by the infamous OilRig …

A quick dive into the murky world of cyberespionage and other growing threats facing managed service providers – and their customers.

Sophos Announces Sophos X-Ops.

ESET’s detection and response capabilities tested in MITRE Engenuity ATT&CK Evaluations.

ESET Threat Report: Attempts to exploit MS Exchange and massive waves of password guessing were the most frequent intrusion vectors.

Tenable Research Reveals Over 40 Billion Records Were Exposed in 2021 almost a 78% increase on 2020.

UAE: Industrial control systems spyware and malicious scripts on the rise in H1 2021.

Tim Taylor QC, Managing Partner at King & Wood Mallesons Dubai, has penned a forensically in-depth op-ed on the rivalry …
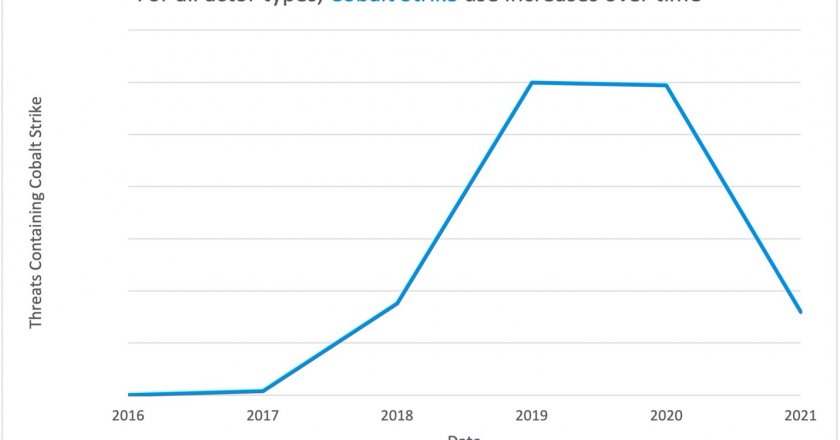
Cobalt Strike: Favorite Tool from Advanced Persistent Threat (APT) to Crimeware.

The global median dwell time, defined as the duration between the start of a cyber intrusion and it being identified, …

The United States has reportedly charged four Chinese military hackers for the 2017 Equifax data breach.

ThreatQuotient senior vice president of strategy Jonathan Couch discusses how enterprises can pull strategic value from threat intelligence.

While external cyber risks are devastating there is a growing number of organisations are concerned about security risks resulting from insiders.

Kaspersky researchers have shared their vision on Advanced Persistent Threats (APTs) in 2020, pointing out how the landscape of targeted attacks will change in the coming months.
In an exclusive interview with TahawulTech.com, Huawei USA chief security officer Andy Purdy discusses the US government’s treatment of the Chinese ICT company.

Amir Kanaan, managing director, META, Kaspersky, discusses the firm’s latest blockchain-based innovations.

The ongoing trade war between the United States and China shows no signs of reaching a resolution as negotiations between the two global economic superpowers remains deadlocked. However, the topic of technology has now temporarily displaced the thorny subject of tariffs as the main currency in the dialogue between officials in Beijing and Washington, with the US, launching an aggressive offensive against major technology players in China.

In a bid to ensure transparency and data integrity, Kaspersky Lab is moving a number of its core processes from Russia to a brand-new Transparency Centre. Based in Zurich, Switzerland, the new facility reflects the company’s determination to assure trustworthiness of its products, services and internal processes.