The head of the malware analysis team at antivirus vendor Kaspersky said last week that a recently found exploit that …
The head of the malware analysis team at antivirus vendor Kaspersky said last week that a recently found exploit that …

Microsoft and Symantec on Wednesday announced that they have dismantled a botnet that took over millions of computers for criminal …
Is there really any need for a touch-screen phone with a 5.5-inch display? Plenty must think so, given the sales …

A cyber espionage network has been allowed to flourish in Eastern Europe, former Soviet republics and Central Asian countries since …

Though U.S. officials have consistently blamed Iran for the ongoing stream of distributed denial of service attacks (DDoS) against major …

Security researchers have presented proof-of-concept code capable of accessing the database driving a Microsoft ERP system and then diverting …

Technology has filtered down to infiltrate every part of our routine life and society at large. The Year 2012 …
Make no mistake: When you first launch iTunes 11, it’s going to feel awfully different from the iTunes you’ve grown accustomed …

According to a recent study ‘The Five Faces of the Cloud’ by Bain & Company, revenue from sales of …

Some cloud providers fail to detect and block malicious traffic originating from their networks, which provides cyber criminals with an …

CoDeSys, a piece of software running on industrial control systems (ICS) from over 200 vendors contains a vulnerability that allows …

HP has rolled out, what it claims is, the industry’s first open-standards-based software-defined network (SDN) technologies to span infrastructure, control …

The ‘denial of service’ attack that disrupted the Wells Fargo & Co. electronic banking operations was the fourth since in …
Microsoft has taken its server OS a giant step forward with yesterday’s release of Windows Server 2012, making this version …

Future warfare could be fought by soldiers using bullets and bombs as well as people hunched over laptops according to …

Dubai is no stranger to having to proactively adjust its approach to expanding technologies. With the integration of ICT in …

A sophisticated cyber surveillance tool that monitors financial transactions with Middle Eastern banks was ‘probably’ built by or …

Storage integrator Proact has launched Probox, a new file-sharing and storage service claiming to be a “Dropbox for the …

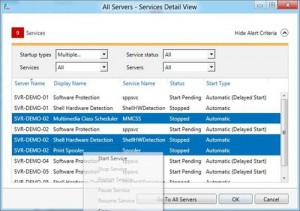
Microsoft has released a free tool to help system administrators, IT security professionals and software developers understand how newly installed …
Far more than Apple’s “version of Word,” Pages is full of powerful, time-saving features that help you make great word …