Cybercrimes and information security breaches discriminate no one, and the healthcare sector is no exception. With enhanced data storage of …


Cybercrimes and information security breaches discriminate no one, and the healthcare sector is no exception. With enhanced data storage of …
Within the average large enterprise, sensitive data is being shared to generative AI apps every hour of the working day.

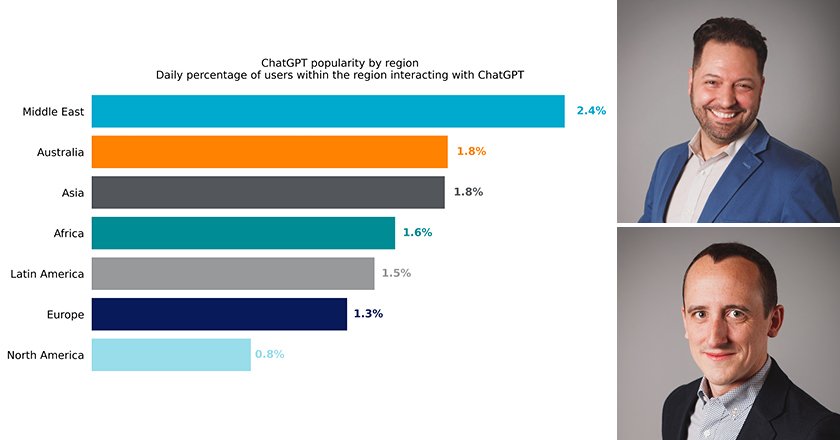
This spike reflects a similar trend in the Middle East region, which projected a two-fold hike (103%) in Rootkit detections, as compared to the first five months of last year.

Fady Younes, Cybersecurity Director, EMEA Service Providers and MEA, Cisco has penned a thought-leadership article that provides businesses and employees …

Attacks on Middle Eastern government agencies are mainly carried out by APT groups (56%), covertly establishing themselves in the victim’s infrastructure for the purpose of cyberespionage.

With at least 75% of Organisations Upgrading Infrastructure and 78% Increasing Security Budgets, OPSWAT’s Latest Report Highlights Disparity Between Infrastructure Upgrades, Spending and Security Improvements.

Behavioural correlation of events from multiple sources helps to act faster, get more attack context and start looking for previously unseen activities.

Vibin Shaju, VP Solutions Engineering EMEA at Trellix, explains how XDR is crucial for cybersecurity in GCC as organizations seek …

Ransomware is the only form of cryptocurrency-related crime that has grown in 2023, with attackers on pace for their second-biggest year ever.

Kaspersky unveils a comprehensive report highlighting the increasing peril faced by small and medium-sized businesses (SMBs) in the current cyberthreat landscape.

Pure Storage, a leader in advanced data storage technology and services, has announced a first of its kind ransomware recovery …
Proper configurations of a security solution are crucial to prevent it from disabling or even abusing it – a tactic often seen to be employed by APT groups/actors.

The UNIFY by Help AG platform unifies the capabilities of visibility, collaboration, orchestration and automation for a seamless user experience and consistent service delivery.

Each scenario demonstrates the cybersecurity’s true role in terms of business continuity and profitability, highlighting emerging challenges and threats.

Zeki Turedi, CTO, EMEA at CrowdStrike has penned a thought leadership article which outlines how ‘identity’ holds the key to …
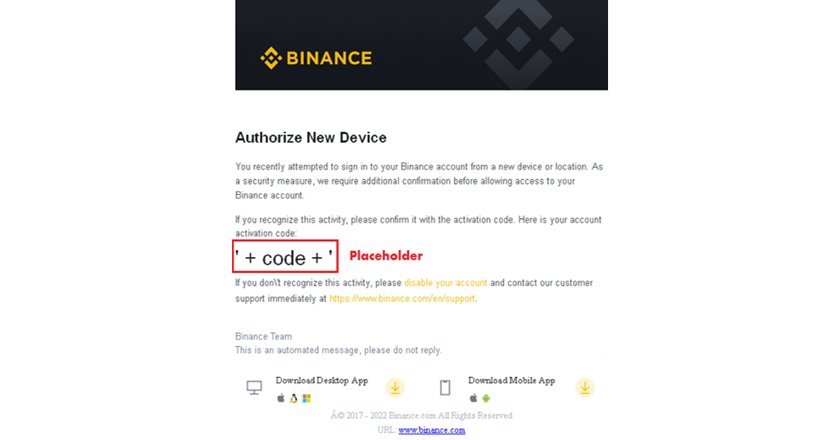
A series of malicious actions allow the extension to run stealthily while the user is browsing the internet. As a result, threat actors become capable of transferring the BTC from the victim’s wallet to their wallet using web injections.
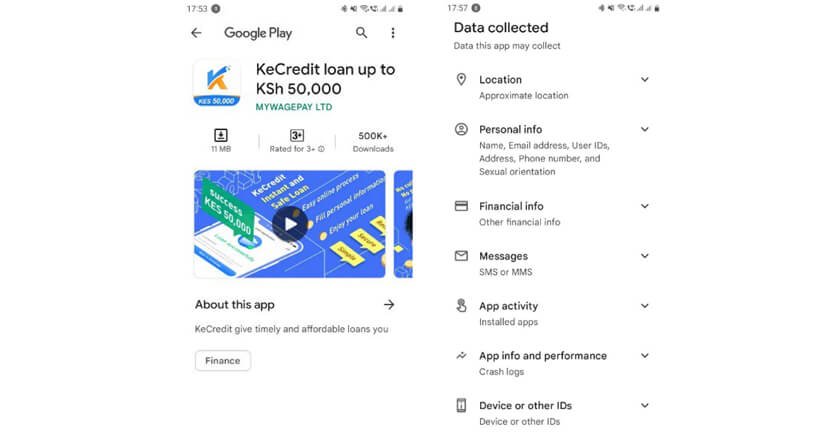
Kaspersky experts continuously monitor the mobile threat landscape and track threat trends to provide the most up-to-date intelligence about the potential dangers.

According to recent research, more than 85% of companies have been the victim of a ransomware attack in the past year.

GBS’ cloud portfolio offers scalability, flexibility, cost-efficiency, and accessibility to resources on-demand,

OPINION: Tarek Naja, Solutions Architect, at Qualys, believes that in order to overcome the complexities that come with moving workloads …