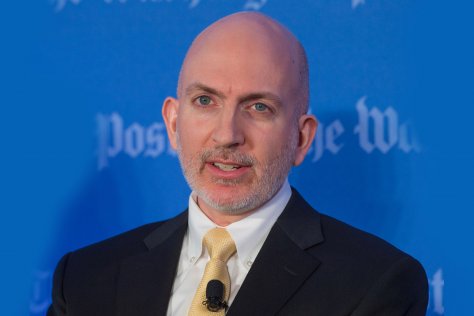
Principal security strategist Richard Bejtlich discusses how organisations can leverage Corelight to bolster both their preventive and proactive security strategies.
Corelight is primarily leveraged for security use cases such as threat hunting with its network transaction logs. Can you explain what are the use cases for Corelight?
First, Corelight, on its own, is a completely passive system. It is an observation platform, from which one can understand the network. No one is going to degrade, disrupt, or otherwise impair the network by properly deploying Corelight. The system simply listens for traffic provided by a network tap, traffic broker, switch span port, or virtual private cloud traffic mirroring source.
Second, Corelight’s transaction logs are essentially compact, high-fidelity descriptions of how the network is being used. Its data is inherently “policy neutral,” meaning that the software observes, distills, and records what it sees, regardless of whether an outsider considers it good, bad, or indifferent. “Out-of-the-box” Corelight is keeping track of what it sees, working as a platform upon which many network-centric capabilities can be built.
Third, Corelight retains data that its programmers have found to be most useful for those trying to understand their network. Corelight gives administrators, engineers, analysts, scientists, and others, the data they need in a format they can most efficiently use. For example, when working with Javascript Object Notation (JSON) formatted output, the logs are essentially self-documented text files, readable by humans and easy-to-share for collaborative analysis.
Now that we know that Corelight is a passive system, describing network use, and offering the right data for analysis, what are the other applications for Corelight that goes beyond threat hunting?
Let me give you an example that’s based on a real event and is applicable to many organisations.
A component of a global company wanted to tighten up the security systems between itself and the firm’s other business units. This division wanted to restrict network access to those parties who required it for business purposes, while denying access to everyone else. However, the division did not know how its network was being used. It feared that if the security team began implementing new access control list entries on in-line security devices, primarily routers and firewalls, that legitimate business traffic might be disrupted. The division worried that interruptions to business operations would undermine its security measures and result in no improvement whatsoever.
The security team realised that it needed to understand how its network was being used before implementing a single new access control list. They began collecting network security monitoring data in Corelight format at the locations where they expected to begin limiting network access. After 30 days, they analysed the data and developed a profile for normal business-to-business activity, which in the future would be whitelisted and passed. They also discovered several instances of suspicious and malicious activity which prompted formal incident response processes.
Once the analysis was complete, the security team implemented their new access control list, based on the 30 days of transaction logs. They did not hear a single complaint from any business representative. They had successfully improved the security of their business-to-business network connections while preserving legitimate operations. They decided to replicate the process in other parts of the company as well.
The scenario you have described looks like an example of organisation implementing a preventive security measures, which means the business unit was trying to improve its posture. Can Corelight be instrumental for organisations that are on the other end of the spectrum and want to apply proactive security strategies?
Absolutely, a previously stated, Corelight data is compact, yet high-fidelity. In one experiment that I conducted, I found that Corelight data was 1/1000th the size of full content data in libpcap format (“pcap”). In other words, I had collected roughly 300 GB of network data in pcap format over two weeks, but Corelight summarised that data into logs occupying 300 MB of space, in a compressed and archived format (“gzip”).
Some believe that security teams should only collect the data that they could reasonably be expected to review on a regular basis. The special nature of Corelight data turns this advice on its head. Because raw storage is cheap, it makes sense to collect Corelight data whether or not it is immediately or routinely reviewed.
Consider the benefit of having weeks, months, or potentially years of Corelight data saved to disk. If at some point the organisation suspects it has been compromised, that data will be invaluable. Using Corelight data, organisations conducting incident response can better determine the scope and duration of the incident, stretching back as far as the stored data allows.
One caveat to this strategy is important: beware cost or storage limitations imposed by a Security and Information Event Management (SIEM) solution. It does not make sense to load unending data into a SIEM if the cost model is volume-based. The advice here relates to saving to a cheap storage solution, whether an on-premise option or cloud-based offering.
An earlier version of this article mentioned that EMT Distribution is Corelight’s distributor in the region. EMT Distribution is not affiliated with Corelight’s regional operations. The company has not officially announced a distribution partner for the region.





