Gautam Kumar, co-founder and COO, FarEye, elaborates on how advanced logistics can transform customer experiences. The supply chain and logistics …



Gautam Kumar, co-founder and COO, FarEye, elaborates on how advanced logistics can transform customer experiences. The supply chain and logistics …
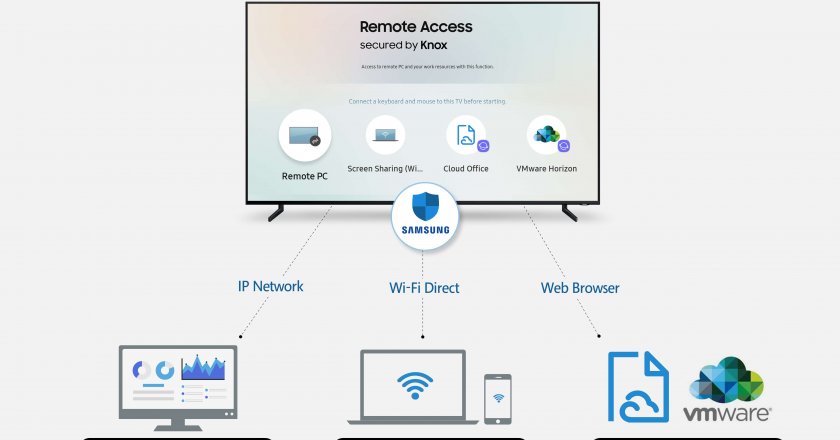
Samsung Electronics has announced Remote Access, a new feature that will be available on its Smart TV lineups starting 2019. …

Microsoft has launched the ‘Make your Wish’ campaign across the Middle East. The initiative calls on individuals and organisations of …

SonicWall has announced its record year-on-year growth in the EMEA region.

Industry experts reveal how technology channel partners can capitalise on the opportunities present in the PC peripherals market.

The American technology giant, Intel Corporation, has awarded NYU Abu Dhabi, NYUAD, a research grant of three years of funding, …

NetApp has concluded its annual, three-day conference to help data visionaries across industries and disciplines create their own data-driven journeys …

Cybersecurity player Fortinet has announced recent customer, partner and market momentum, as well as independent testing results, of its FortiGate …

Regional systems integrator Raqmiyat has achieved International Organization for Standardization (ISO) 9001:2015 certification. By meeting the extensive criteria for these …

What’s stopping global businesses from protecting their assets despite significant investments in cybersecurity programmes? That’s the question we asked ourselves when trying to determine the reasons are behind the dangerous gap in modern IT security.
GET TAHAWULTECH.COM IN YOUR INBOX